Certified Penetration Testing Professional (CPENT)
Elite training from EC-Council designed to test the skills of penetration testers in dealing with complex enterprise infrastructure. This training takes you to the level of real-world pentesting with multi-layered scenarios, advanced pivoting, exploit development, and even IoT and OT security.
Join the Certified Penetration Testing Professional (CPENT) Training
The CPENT program provides hands-on experience in a realistic cyber range. Participants will be tested on mastering end-to-end penetration testing, from planning, exploitation, pivoting, to professional reporting. With international industry standards, CPENT ensures you are ready to face real-world challenges as an elite penetration tester.
Benefits of Joining Training at Temika Cyber
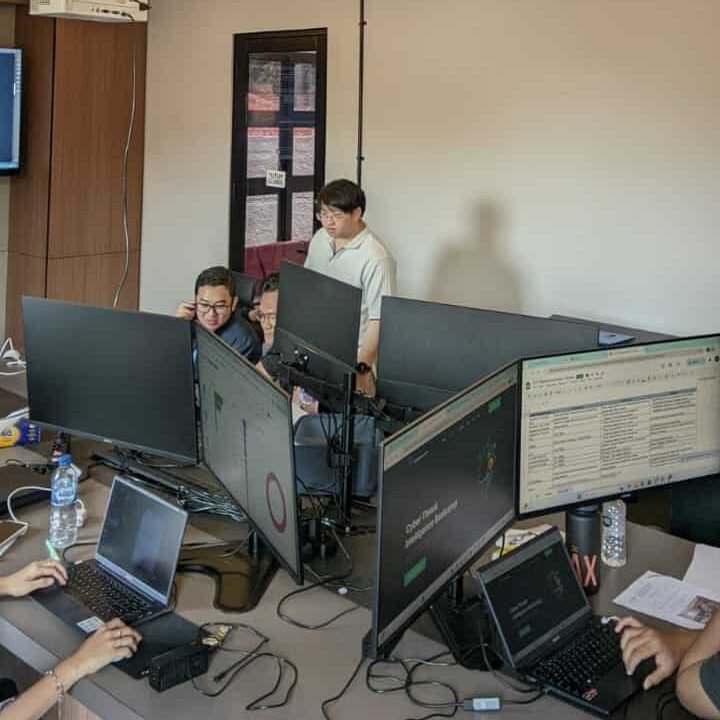
Hands-On Cyber Range
Lab with realistic enterprise infrastructure, segmented network, pivoting, and real-world scenarios.
IoT & OT Security
Focus on the security of IoT devices and OT (Operational Technology) infrastructure.
Exploit Development Training
Learn to create exploits, reverse engineering, and bypass modern protections.
Exam Preparation & Certification Path
Material, strategy, and 24-hour CPENT exam simulation.
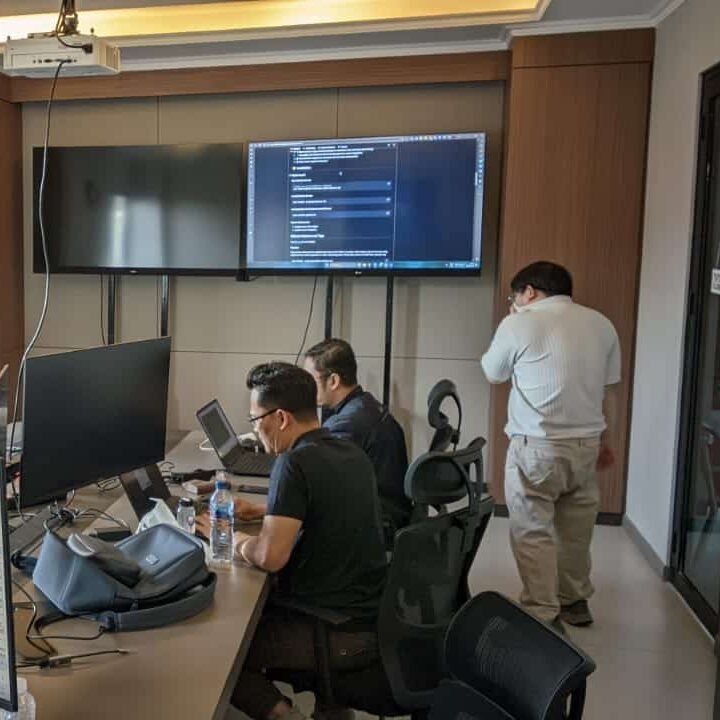
Red Team Simulation
A real attack simulation that tests offensive skills from the beginning to reporting.
Advanced Tools & Frameworks
Use popular tools (Metasploit, Cobalt Strike, Burp Suite, etc.) plus the NIST framework, MITRE ATT&CK.
Why Should One Master CPENT?
🚀 High Industry Standards
CPENT is globally recognized as a benchmark for advanced penetration tester skills.
🎯 Combination of Pentest Skills
Training in exploit development, privilege escalation, and advanced security bypass.
🙋Elite Career Opportunities
Opening access to high-demand positions such as senior pentester, red team lead, and cyber consultant.
Jadwal Pelatihan
Pelatihan dimulai
Program Akan dilaksanakan secara: –
Periode Kelas: –
Estimasi Durasi Belajar: –
Training Objectives
After successfully completing this course, participants will be able to:
-
Mastering advanced penetration testing from reconnaissance to reporting.
-
Understanding how to perform pivoting on a segmented network.
-
Improving exploit development and privilege escalation skills.
-
Mastering cloud security, IoT, and OT.
-
Applying framework standards (MITRE ATT&CK, NIST, OWASP).
-
Prepare a professional pentest report that is acceptable to management.
-
Passed the CPENT exam and obtained international certification.
Syllabus
- 09:00 – 09:30: Welcome & Course Introduction
- Introductions and setting expectations.
- Overview of CPENT program and exam format (24-hour challenge).
- 09:30 – 10:45: Module 01 – Advanced Footprinting & OSINT
- Active vs. passive reconnaissance.
- Advanced OSINT collection with Maltego, Shodan, and Recon-ng.
- Hands-on Lab: Mapping enterprise targets using OSINT tools.
- 10:45 – 11:00: Morning Break
- 11:00 – 12:30: Module 02 – Network & Service Enumeration
- Scanning internal and external networks.
- Enumerating services, users, and applications.
- Hands-on Lab: Nmap and custom scanning scripts.
- 12:30 – 13:30: Lunch Break
- 13:30 – 15:00: Module 03 – Vulnerability Assessment
- Identifying and prioritizing vulnerabilities.
- Scanning with Nessus, OpenVAS, and custom scripts.
- Hands-on Lab: Vulnerability scanning in segmented networks.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 04 – Exploitation Basics
- Fundamentals of exploit development.
- Exploiting web apps and services.
- Hands-on Lab: Custom exploit execution.
- 16:45 – 17:00: Day 1 Wrap-up & Q&A
- 09:00 – 10:30: Module 05 – Windows Privilege Escalation
- Privilege escalation techniques in Windows.
- Bypassing UAC, exploiting misconfigurations.
- Hands-on Lab: Gaining SYSTEM privileges.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 06 – Linux Privilege Escalation
- Privilege escalation methods in Linux environments.
- Kernel exploits, SUID misconfigurations.
- Hands-on Lab: Exploiting Linux for root access.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 07 – Exploit Development
- Buffer overflows and shellcode injection.
- Reverse engineering applications.
- Hands-on Lab: Writing and testing custom exploits.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 08 – Case Study: Exploit Chain Attack
- Simulated attack chaining multiple vulnerabilities.
- 16:45 – 17:00: Day 2 Wrap-up & Q&A
- 09:00 – 10:30: Module 09 – Pivoting Techniques
- Pivoting in segmented networks.
- SOCKS tunneling, SSH pivoting, proxy chains.
- Hands-on Lab: Moving laterally across networks.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 10 – Active Directory Exploitation
- Kerberoasting, Pass-the-Hash, and Golden Ticket attacks.
- Hands-on Lab: Exploiting AD for domain admin access.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 11 – Cloud & Hybrid Attacks
- Attacking AWS, Azure, and hybrid networks.
- Hands-on Lab: Exploiting cloud misconfigurations.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 12 – Case Study: Multi-Layered Attack
- Simulating a full-scale enterprise breach.
- 16:45 – 17:00: Day 3 Wrap-up & Q&A
- 09:00 – 10:30: Module 13 – IoT Device Exploitation
- Exploiting IoT protocols and devices.
- Hands-on Lab: IoT firmware reverse engineering.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 14 – ICS/SCADA Security
- Industrial Control Systems attack vectors.
- Hands-on Lab: Simulated SCADA exploitation.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 15 – Web & API Exploitation
- Advanced SQLi, RCE, SSRF, and API testing.
- Hands-on Lab: Exploiting APIs in enterprise applications.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 16 – Wireless & Mobile Attacks
- Attacking Wi-Fi, Bluetooth, and mobile apps.
- Hands-on Lab: Rogue AP and mobile exploitation.
- 16:45 – 17:00: Day 4 Wrap-up & Q&A
- 09:00 – 10:30: Module 17 – Red Teaming & Adversary Simulation
- End-to-end attack simulation and reporting to stakeholders.
- Hands-on Lab: Simulated red team operation.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 18 – Reporting & Documentation
- Professional penetration testing reports.
- Mapping findings to MITRE ATT&CK.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 19 – CPENT Exam Strategies
- Exam structure and scoring methodology.
- Time management for 24-hour exam.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 20 – Mock Assessment & Q&A
- Practice exam and feedback session.
- 16:45 – 17:00: Course Wrap-up & Certification Guidance
Meet Your Expert
Trainer 1
Ethical Hacker
Trainer 2
Ethical Hacker
What Do They Say About This Training






Our Professional Certification
Get Special Prices During the Promotion
Early Bird I
- Intensive Training (5 Days)
- Official EC-Council Exam Voucher
- Official Training Material (e-Courseware)
- Official iLabs Access
- Certificate of Attendance
FAQ
They have entrusted it to us