DevSecOps Engineer Training
Build a career in modern application security with a DevSecOps approach. Master secure CI/CD pipelines, security automation, and best practices for integrating security into every stage of the software development lifecycle (SDLC).

Join DevSecOps Engineer Training
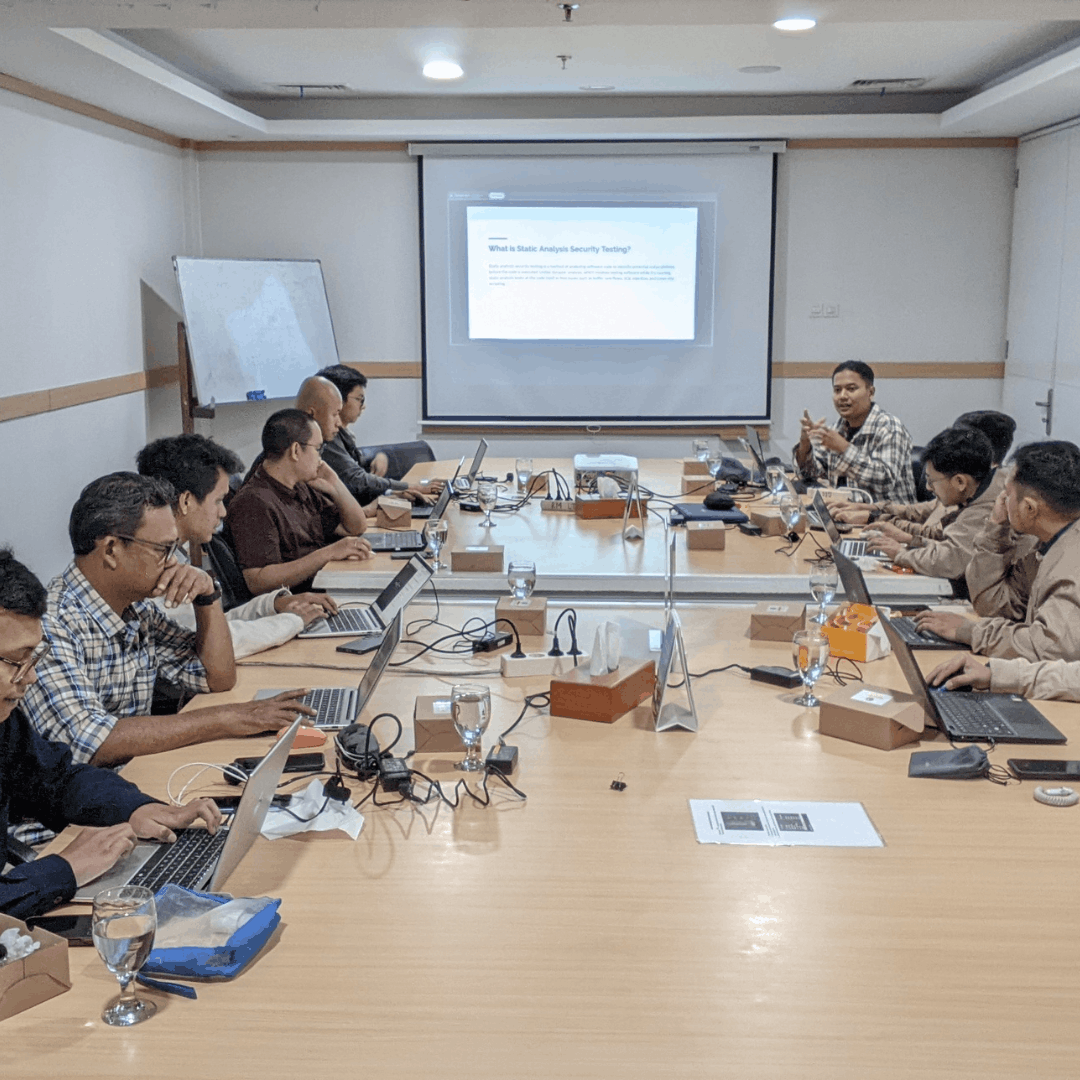
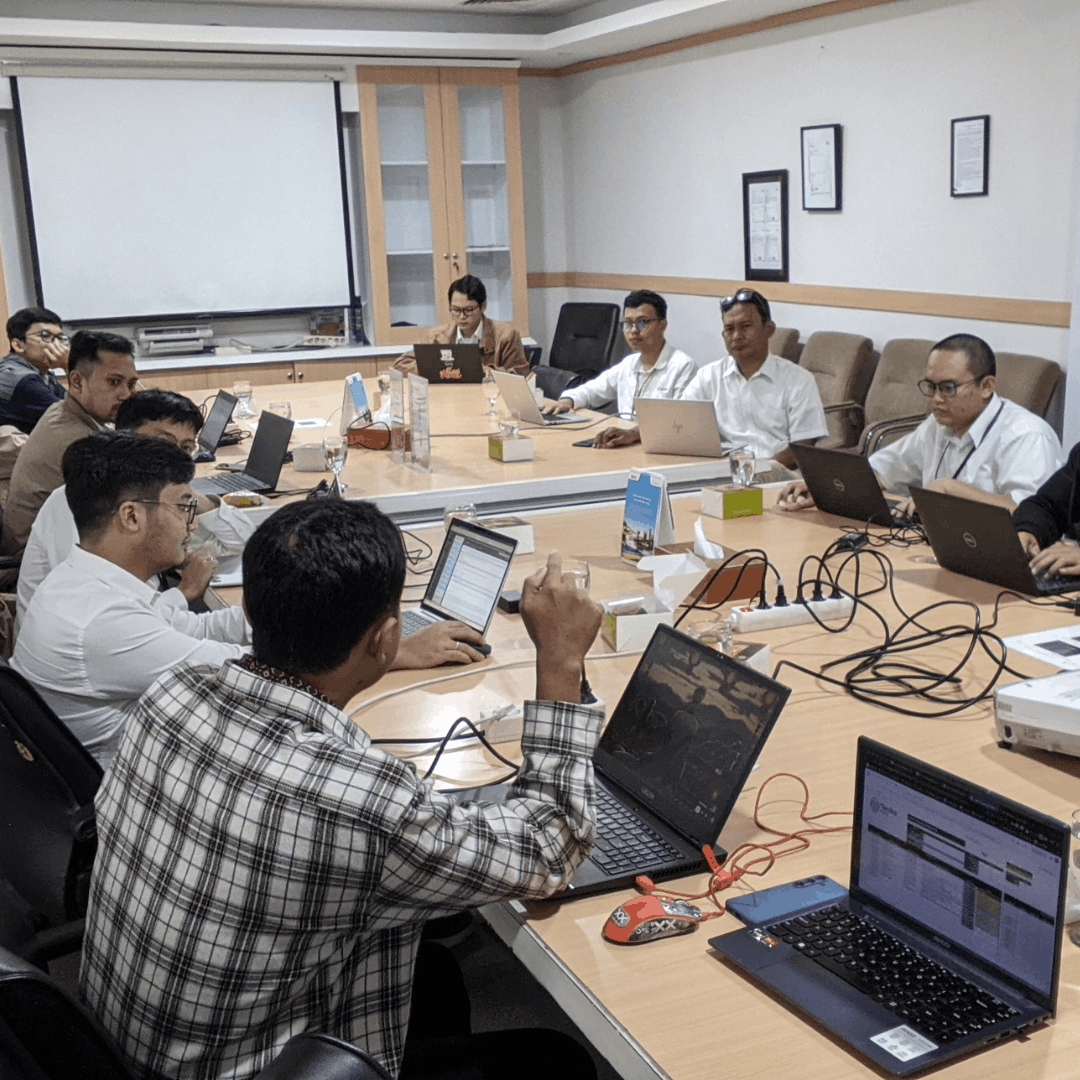
This DevSecOps Engineer training is designed to equip participants with technical and practical skills in integrating development, security, and operations. Participants will learn about secure SDLC concepts, the implementation of automation tools, and how to build a security-first culture within the team.
Benefits of Joining Training at Temika Cyber
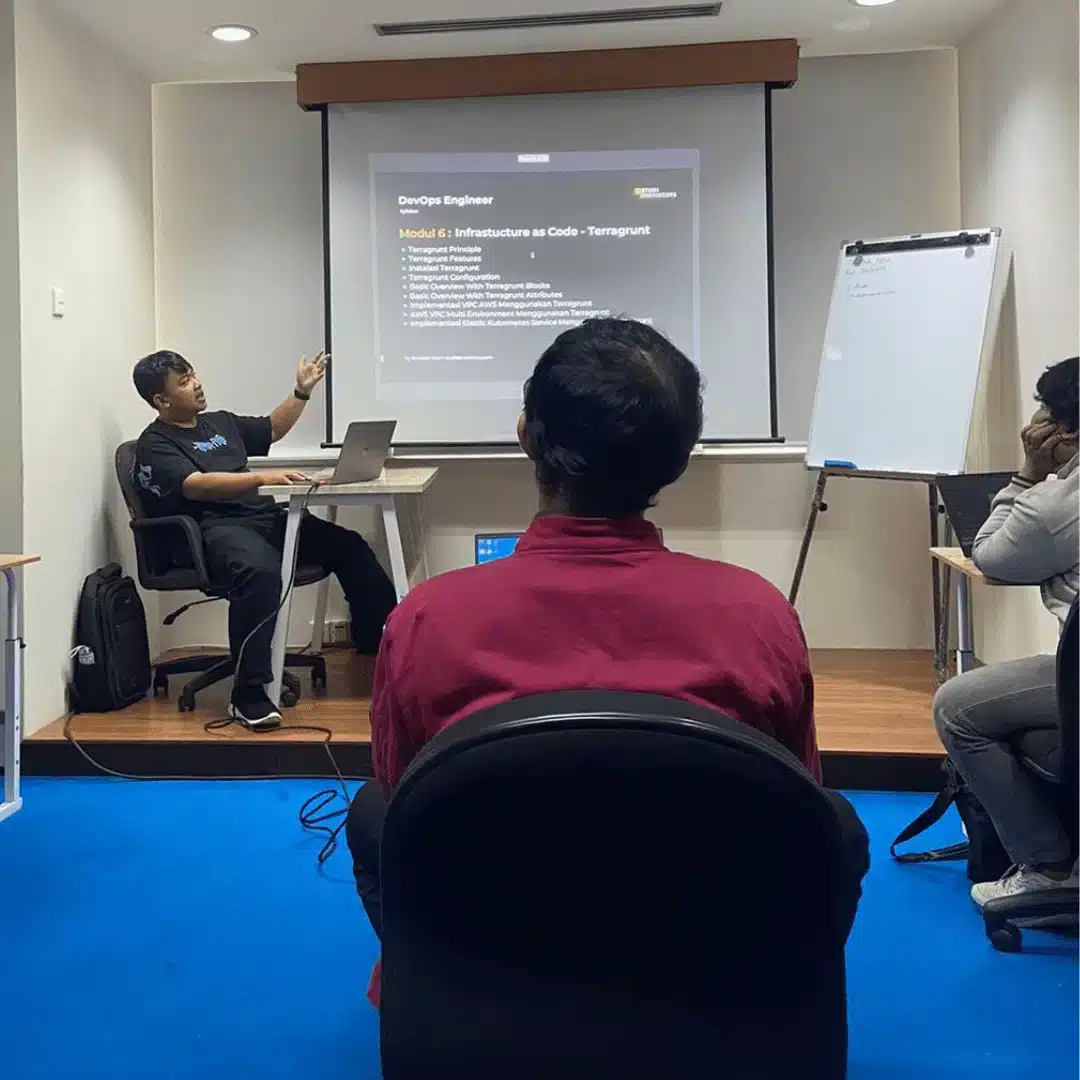
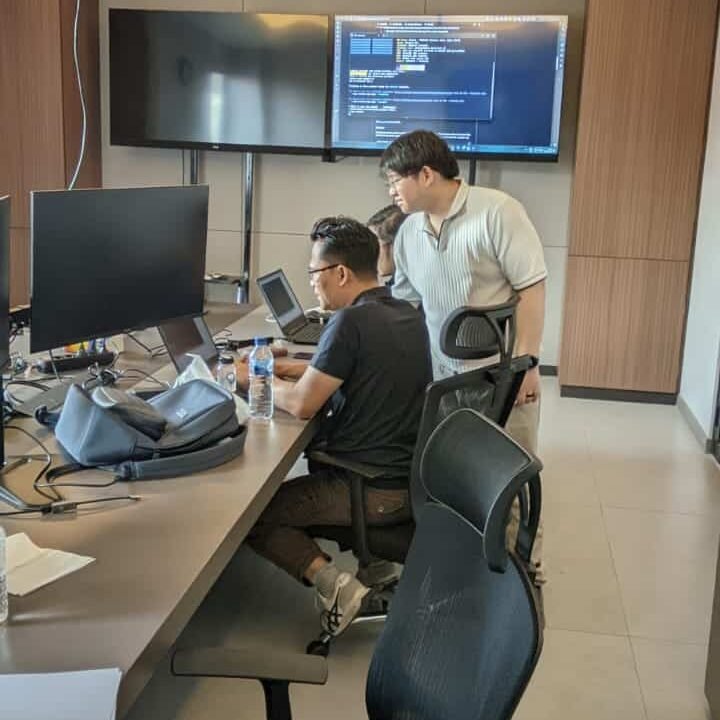
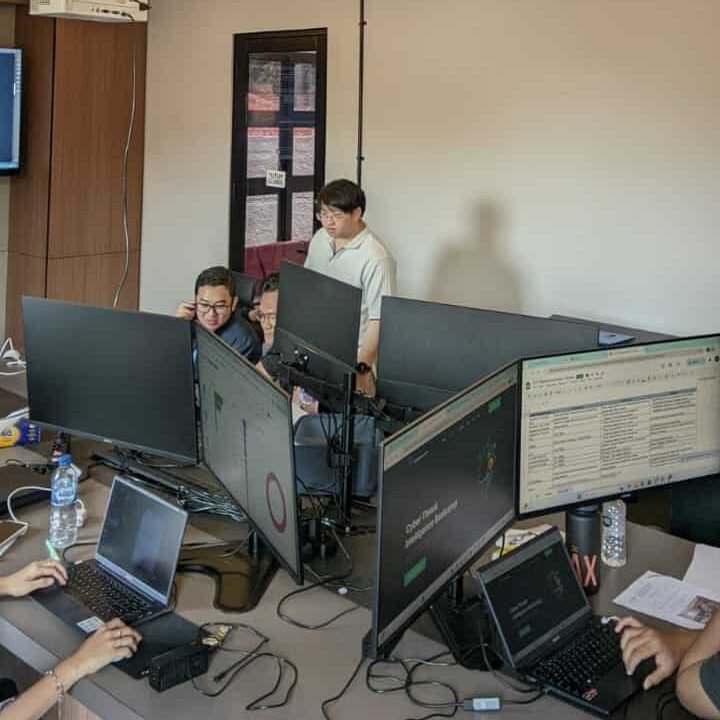
Hands-on Lab with a real CI/CD pipeline
Participants learn to secure the Continuous Integration/Continuous Deployment flow through real practices, not just theory.
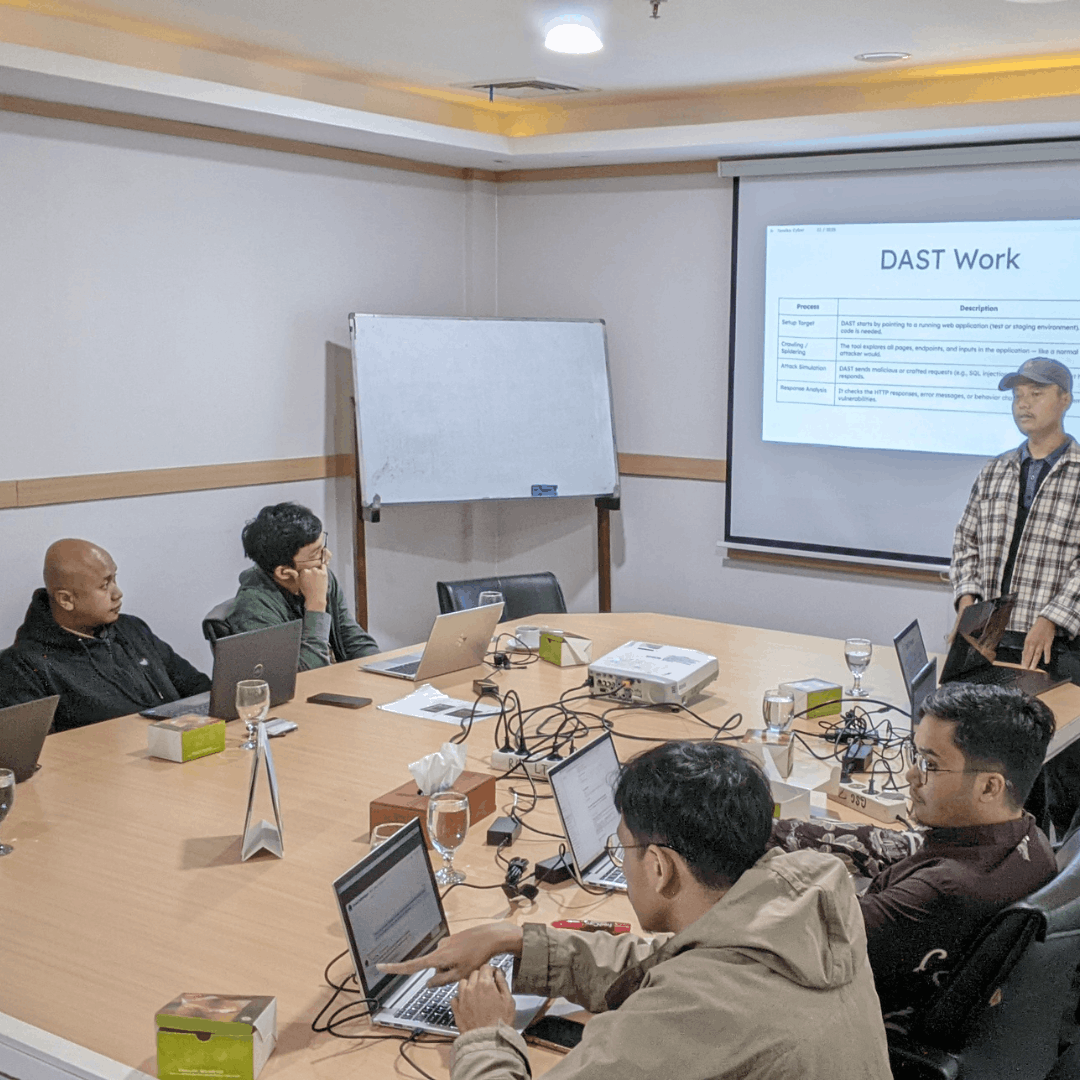
Simulation of security tools integration (SAST, DAST, container scanning)
Studying the use of automated security tools for applications and containers to detect potential vulnerabilities more quickly.
Official graduation certificate from Temika Cyber
Participants receive officially recognized proof of competency, useful for career development and professionalism.
Case study of DevSecOps implementation in a large company
Analysis of real practices from large organizations, so that participants understand the challenges and solutions applied in the professional environment.
Experienced mentor in the fields of DevOps & Security
Guided by experts with firsthand experience in DevOps and cybersecurity, providing insights into best practices and career tips.
Material according to global industry standards
The content is developed following international DevSecOps practices and frameworks, ensuring relevance to global market needs.
Why Should We Master DevSecOps?
🚀 Enhancing the most sought-after cybersecurity skills.
The company now needs engineers who are skilled in security in the DevOps pipeline.
🎯 Reducing the Risk of Attack
DevSecOps helps identify and close security gaps from the early stages of development.
⚡Efficiency & Delivery Speed
Automated security integration increases the speed of software releases without compromising security.
Jadwal Pelatihan
Pelatihan dimulai
Program Akan dilaksanakan secara: –
Periode Kelas: –
Estimasi Durasi Belajar: –
Training Objectives
After successfully completing this course, participants will be able to:
-
Understanding the basic principles of DevSecOps.
-
Able to build a secure CI/CD pipeline.
-
Mastering the integration of security tools in the SDLC.
-
Identifying vulnerabilities from the early stage of development.
-
Securing cloud-based applications & containers.
-
Building a collaborative culture between Dev, Sec, and Ops.
-
Ready to face real-world challenges in DevSecOps implementation.
Silabus
- Module 01 – Introduction To DevSecOps
- DevOps In Depth
- Introduction To DevSecOps
- Framework of DevSecOps and Advantages
- Module 02 – Introduction To DSOMM
- Introduction To DSOMM
- Understanding DSOMM
- Module 03 – Introduction To Cybersecurity
- Introduction To Cybersecurity
- Vulnerability Chain
- False-Positive
- Module 04 – Secure SDLC
- Introduction To Secure SDLC
- Structural Of Secure SDLC
- Flow And Operation Of Secure SDLC
- Module 05 – Methodology Of DevSecOps
- Introduction To SS
- Software Composition Analysis
- Static Application Security Testing
- Dynamic Application Security Testing
- Runtime Application Self Protection
- Introduction To Vulnerability Management
- Introduction To Alert And Monitoring
- Module 06 – Secret Management
- Understanding Secret Management
- Understanding Secret Scanning
- How To Protect Your Secret
- Module 07 – Security Supply Chain With SCA
- Introduction To Software Compositions Analysis
- Pros And Cons SCA
- Vuln DB
- CVE, CWE And PoC
- Module 08 – Static Application Security Testing (SAST)
- Introduction To Static Application Security Testing
- Pros And Cons SAST
- SAST At Pipeline
- Module 09 – Secure SDLC And DAST
- Introduction To DAST
- Pros And Cons DAST
- Module 10 – Auditing / Compliance
- About Compliance
- Automation Compliance
- Golden Image Standard Compliance
- Compliance At Many Environment
- Module 11 – Vulnerability Management
- Introduction To Vulnerability Management
- Integration Of Methodology
- Maintenance Of Finding
- Management For Finding
- Module 12 – Security On Cloud
- Introduction To Security On Cloud
- How To Secure Your Cloud
- Feature For Secure Your Cloud On AWS
- Module 13 – Security On Mobile Apps
- Introduction To Secure Mobile Apps
- How To Secure Your Mobile Apps
- Module 14 – Security On Web Apps
- Introduction To Secure Web Apps
- How To Secure Your Web Apps
- Module 15 – Final Project
- Integrate security practices from cloud, mobile, and web applications into a CI/CD pipeline.
- Simulated real-world DevSecOps scenario to implement end-to-end security.
- Hands-on lab: Identify vulnerabilities, apply SAST/DAST, and deploy secure pipeline.
Meet Your Expert
Trainer 1
Ethical Hacker
Trainer 2
Ethical Hacker
What Do They Say About This Training






Our Professional Certification

Get Special Prices During the Promotion
Early Bird I
- Intensive Training (5 Days)
- Official Training Material (e-Courseware)
- Official iLabs Access
- Certificate of Attendance
FAQ
They have entrusted it to us