5 Days Intensive Training: Certified Ethical Hacker (CEH) v13 Training
Improve your ethical hacking skills with EC-Council global standards.

Join the Certified Ethical Hacker (CEH) v13 Training
The official ethical hacking training program from EC-Council that is internationally recognized. Participants will learn directly about the five main phases of hacking, from reconnaissance, gaining access, to covering tracks, with intensive lab practice. The latest version CEH v13 is equipped with the tools, techniques, and methodologies currently used by hackers and cybersecurity professionals in the real world, making it ideal for anyone looking to advance their career in the field of cybersecurity.
Benefits of Joining Training at Temika Cyber
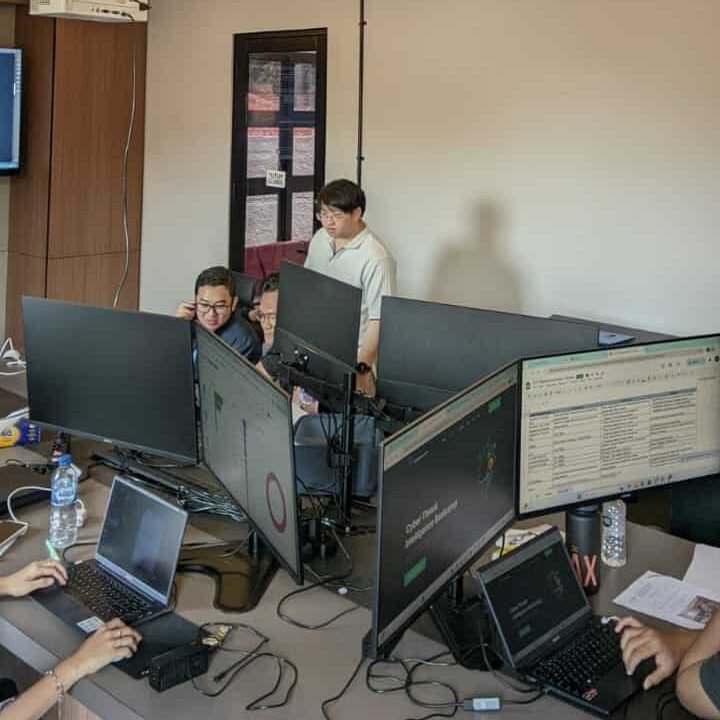
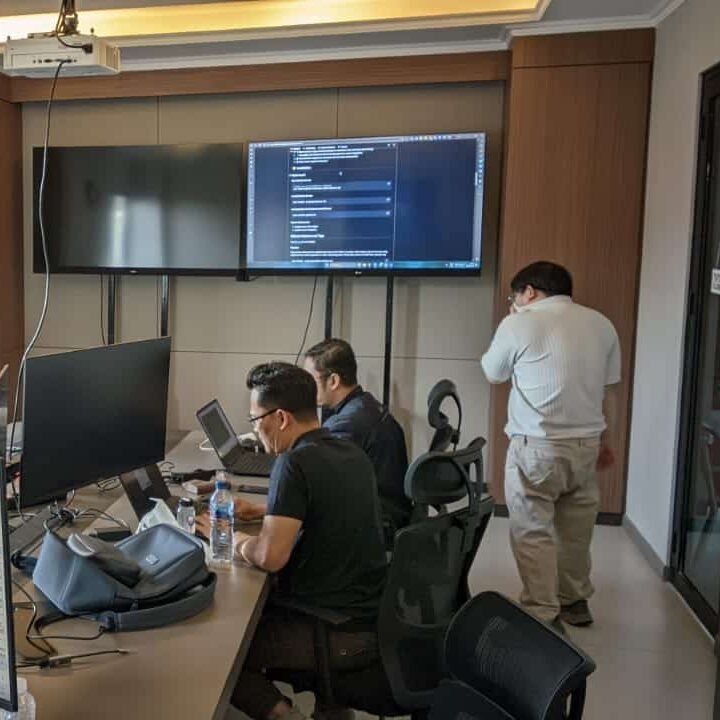
Hands-on Lab & Real Attack Simulation
Follow scenario-based training. Learn hacking techniques from reconnaissance to exploitation with a safe virtual environment.
Latest CEH v13 Official Materials and Curriculum
The curriculum meets the EC-Council standards and covers 20 important domains: malware, cloud security, IoT, ransomware, and emerging threats.
Exam Preparation & Certification Path
Get tips, practice questions, and guidance to be ready for the official CEH v13 exam and achieve international certification.
Expert Instructors & Mentoring Support
Learn directly from experienced cybersecurity practitioners who are ready to guide and answer your technical questions.
Career-Ready Skills & Networking
Master the skills sought by global companies: penetration testing, vulnerability assessment, security audit. Build a portfolio and professional network.
Exclusive Alumni Community & Resources
Access to the Temika Cyber alumni community for discussions, material updates, job opportunities, and real-world collaboration.
Why Should You Master Certified Ethical Hacker (CEH) v13?
🚀 High Demand
The demand for cybersecurity professionals, particularly ethical hackers, continues to rise. The need for security analysts is projected to grow by 32% in this decade, with wide career opportunities and long-term prospects across various industries.
💰 Competitive salary
Ethical hacking skills are highly valuable, with an average salary of $121,875 per year in the US; even beginners can start from $112,000 proving that learning CEH is a genuine career investment.
⚡ Increasing Cyber Threats
Cyber attacks are becoming increasingly complex: ranging from malware, ransomware, AI-based attacks, to cloud and IoT exploitation. By mastering CEH v13, you not only understand how hackers operate, but also are capable of detecting, preventing, and responding to threats with a proactive approach.
Training Objectives
After successfully completing this course, participants will be able to:
-
Understanding and applying the principles of ethical hacking and cybersecurity comprehensively.
-
Performing footprinting and reconnaissance for a complete analysis of the target network.
-
Using scanning and enumeration techniques to identify active hosts and open ports.
-
Conducting a vulnerability analysis to identify security gaps in the system.
-
Applying system hacking methodology to gain legitimate access to the system.
-
Understanding the malware lifecycle and analyzing various modern malware threats.
-
Performing network sniffing, social engineering, and Denial-of-Service (DoS) attacks.
-
Understanding and executing session hijacking, attacks on web servers, and web application attacks including SQL injection.
-
Assessing and exploiting wireless networks and mobile platforms.
-
Understanding security challenges in Cloud, IoT, and Operational Technology (OT) environments.
-
Applying cryptographic techniques and understanding their role in maintaining data security.
Syllabus
- 09:00 – 09:30: Welcome, Course Introduction, and CEH v13 Overview
- Introductions and setting expectations.
- The structure of the 5-day training.
- Understanding the CEH certification process and exam.
- 09:30 – 10:45: Module 01: Introduction to Ethical Hacking
- Key concepts: Hacking, Ethical Hacking, Cyber Kill Chain.
- Information Security Controls, Laws, and Standards.
- The Five Phases of Ethical Hacking.
- 10:45 – 11:00: Morning Break
- 11:00 – 12:30: Module 02: Footprinting and Reconnaissance
- Defining Footprinting and its methodologies.
- Using search engines and advanced Google hacking techniques.
- DNS, Whois, and network footprinting.
- Hands-on Lab: Information gathering using Maltego, theHarvester, and other tools.
- 12:30 – 13:30: Lunch Break
- 13:30 – 15:00: Module 03: Scanning Networks
- Network scanning concepts and methodologies.
- Using tools like Nmap and Hping3 for port scanning.
- Scan types: TCP Connect, SYN Stealth, UDP, etc.
- Hands-on Lab: Performing network scans to identify live hosts, open ports, and running services.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 04: Enumeration
- Enumeration concepts and techniques.
- NetBIOS, SNMP, LDAP, NTP, and DNS enumeration.
- Hands-on Lab: Enumerating user accounts, network resources, and services using tools like SuperScan and Hyena.
- 16:45 – 17:00: Day 1 Wrap-up, Q&A
- 09:00 – 10:30: Module 05: Vulnerability Analysis
- Concepts of vulnerability assessment.
- Types of vulnerability assessments and tools.
- Analyzing vulnerability assessment reports.
- Hands-on Lab: Using Nessus/OpenVAS to scan for and analyze vulnerabilities in a target environment.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:30: Module 06: System Hacking
- Methodology: Gaining Access, Escalating Privileges, Maintaining Access, Clearing Logs.
- Password cracking techniques (Brute-force, Dictionary attacks).
- Hands-on Lab: Using the Metasploit Framework to exploit a known vulnerability and gain shell access.
- Hands-on Lab: Using tools like John the Ripper and Hydra for password cracking.
- 12:30 – 13:30: Lunch Break
- 13:30 – 15:00: Module 06: System Hacking (Continued)
- Privilege escalation techniques on Windows and Linux.
- Executing applications and maintaining persistence (backdoors, rootkits).
- Covering tracks: Clearing logs and hiding files.
- Hands-on Lab: Escalating privileges and clearing audit logs.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 07: Malware Threats
- In-depth analysis of Trojans, Viruses, Worms.
- Malware analysis techniques (Static and Dynamic).
- Understanding Ransomware and modern threats.
- Countermeasures against malware.
- 16:45 – 17:00: Day 2 Wrap-up, Q&A
- 09:00 – 10:30: Module 08: Sniffing
- Concepts of sniffing and how it works (MAC flooding, ARP poisoning).
- Passive vs. Active sniffing.
- Tools for sniffing (Wireshark, tcpdump).
- Hands-on Lab: Performing Man-in-the-Middle (MITM) attacks using Ettercap/Cain & Abel and analyzing captured traffic.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:30: Module 09: Social Engineering
- The art of human manipulation: Principles and phases.
- Types of attacks: Phishing, Vishing, Impersonation.
- Insider threats and identity theft.
- Social engineering countermeasures.
- 12:30 – 13:30: Lunch Break
- 13:30 – 15:00: Module 10: Denial-of-Service (DoS/DDoS)
- DoS/DDoS concepts and attack techniques (e.g., SYN Flooding, Smurf attack).
- Understanding Botnets.
- Tools for launching DoS attacks.
- Mitigation and defense strategies.
- Hands-on Lab: Simulating a DoS attack in a controlled environment.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 11: Session Hijacking & Module 12: Evading IDS, Firewalls
- Session hijacking concepts at network and application levels.
- IDS, Firewall, and Honeypot concepts.
- Techniques for evading security mechanisms (e.g., packet fragmentation, using proxies).
- Hands-on Lab: Bypassing a firewall rule set using scanning techniques.
- 16:45 – 17:00: Day 3 Wrap-up, Q&A
- 09:00 – 10:30: Module 13: Hacking Web Servers
- Web server architecture and attack methodologies.
- Attacking misconfigurations and vulnerabilities.
- Website defacement and countermeasures.
- Hands-on Lab: Attacking a misconfigured web server to gain directory access.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:30: Module 14: Hacking Web Applications
- Web application concepts and the OWASP Top 10 vulnerabilities.
- Attacks such as Cross-Site Scripting (XSS), Cross-Site Request Forgery (CSRF), and Broken Authentication.
- Hands-on Lab: Exploiting an XSS vulnerability in a sample web application.
- 12:30 – 13:30: Lunch Break
- 13:30 – 15:00: Module 15: SQL Injection
- Deep dive into SQL injection concepts and types.
- Techniques for finding and exploiting SQL injection vulnerabilities.
- Evasion techniques and countermeasures.
- Hands-on Lab: Using SQLmap to automate the discovery and exploitation of an SQL injection flaw.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 16: Hacking Wireless Networks
- Wireless concepts (WEP, WPA, WPA2, WPA3).
- Wireless threats and attack methodologies.
- Cracking wireless encryption.
- Hands-on Lab: Using the aircrack-ng suite to crack a WPA2-PSK password.
- 16:45 – 17:00: Day 4 Wrap-up, Q&A
- 09:00 – 10:30: Module 17: Hacking Mobile Platforms
- Mobile platform attack vectors (Android and iOS).
- Mobile malware and reverse engineering.
- Mobile security guidelines and tools.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:00: Module 18: IoT and OT Hacking
- Introduction to IoT and OT (Operational Technology) ecosystems.
- Common vulnerabilities and attack methodologies.
- Firmware analysis and exploitation.
- Securing IoT and OT devices.
- 12:00 – 13:00: Lunch Break
- 13:00 – 14:30: Module 19: Cloud Computing
- Cloud computing concepts (IaaS, PaaS, SaaS).
- Cloud security threats and attack vectors (e.g., container vulnerabilities, misconfigured S3 buckets).
- Cloud security best practices and tools.
- 14:30 – 15:30: Module 20: Cryptography
- Cryptography concepts: Hashing, Encryption (Symmetric/Asymmetric).
- Public Key Infrastructure (PKI).
- Common cryptographic attacks.
- 15:30 – 15:45: Afternoon Break
- 15:45 – 17:00: Final Review, Exam Preparation & Course Wrap-up
- Review of the 20 CEH v13 modules.
- Strategies for taking the CEH exam.
- Sample exam questions and discussion.
- Final Q&A and course conclusion.
- Distribution of certificates of attendance.
Meet Your Expert
Trainer 1
Ethical Hacker
Trainer 2
Ethical Hacker
What Do They Say About This Training






Our Professional Certification
Get Special Prices During the Promotion
Early Bird I
- Intensive Training (5 Days)
- Official EC-Council Exam Voucher
- Official Training Material (e-Courseware)
- Official iLabs Access
- Certificate of Attendance
FAQ
The CEH v13 training is suitable for IT professionals, network administrators, security analysts, SOC teams, IT students, and anyone who wishes to pursue a career in the field of cybersecurity.
They have entrusted it to us