Certified Kubernetes Security Specialist (CKS) Training
Develop advanced skills in ensuring the security of Kubernetes clusters, from configuration, networking, to supply chain security.

Join the Kubernetes CKS Training
Kubernetes is the industry standard in container orchestration. However, Kubernetes security has become a major challenge in production environments. This CKS training is designed to help you master best practices in securing container applications, Kubernetes infrastructure, and the entire CI/CD pipeline.
Benefits of Joining Training at Temika Cyber
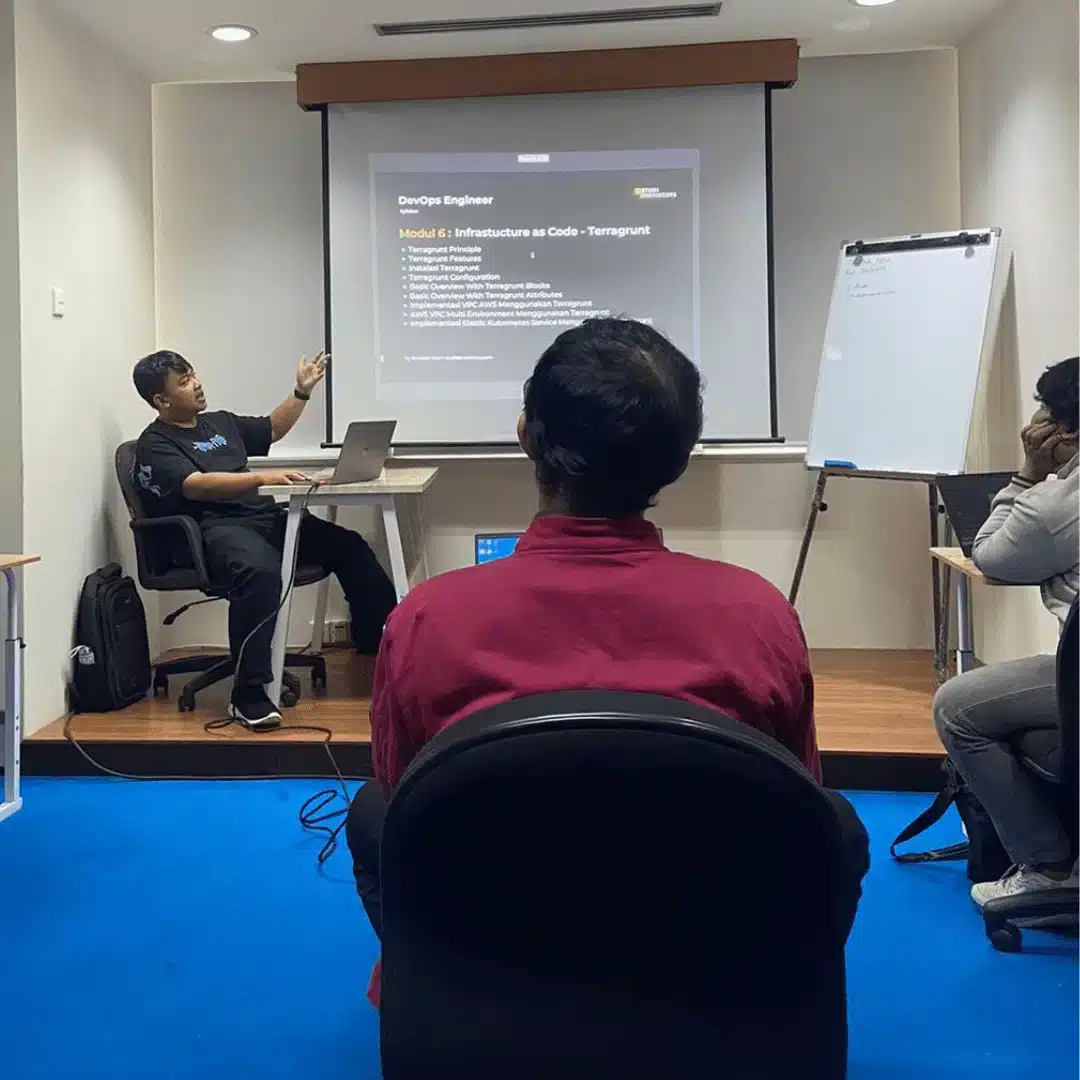
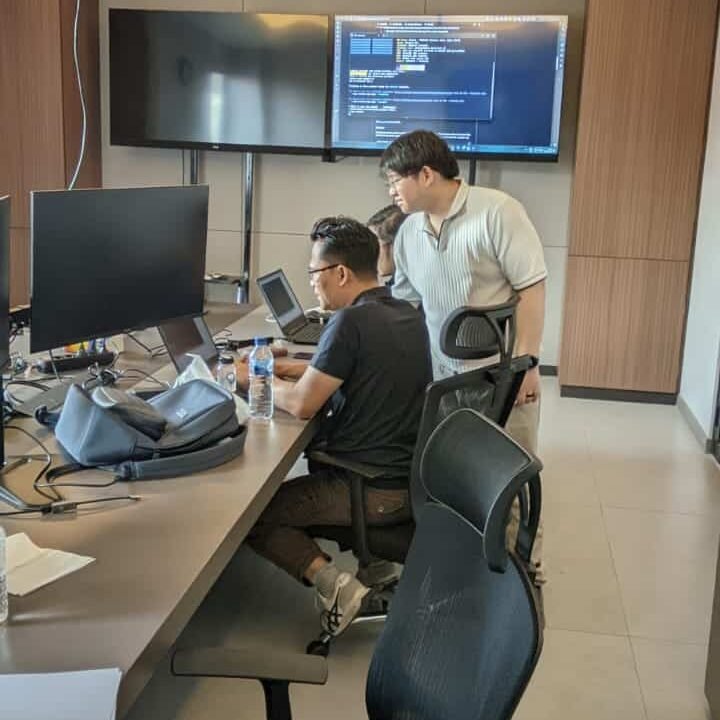
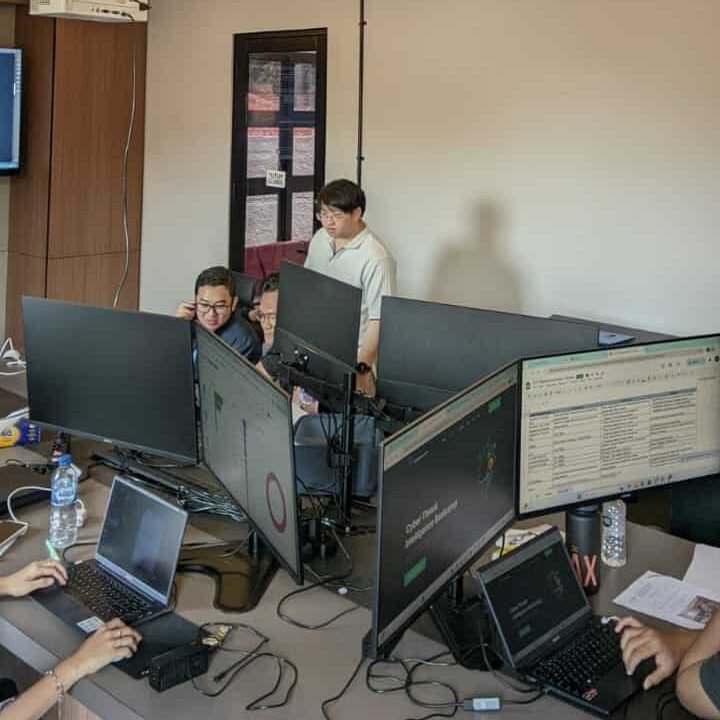
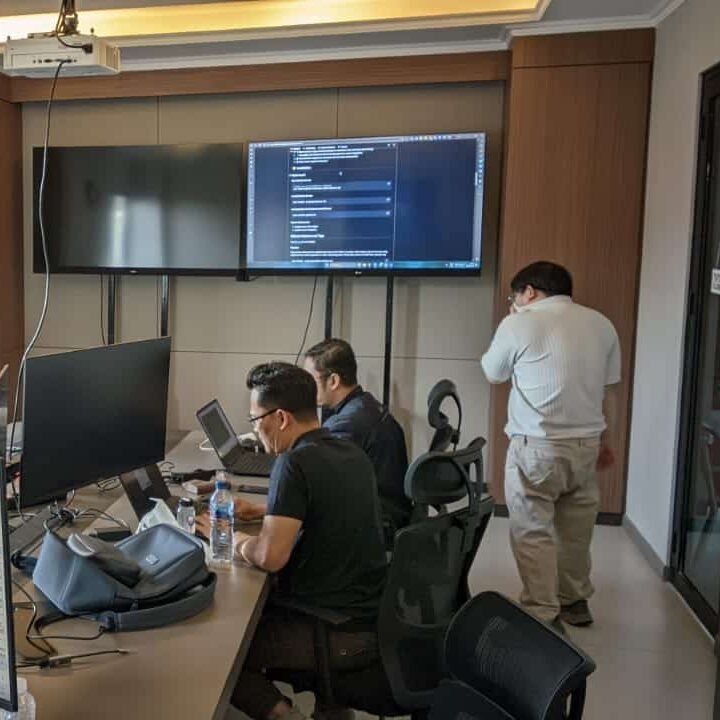
Hands-on Lab Real Cluster
Directly practice in a Kubernetes environment that resembles production.
Kubernetes Security Focus
From configuration, networking, to supply chain & runtime.
Real Case Study
Scenario-based training commonly found in large companies.
Material According to CNCF & CKS Exam Standards
According to the official certification blueprint.
Experienced Mentor
Kubernetes Security & DevSecOps Practitioner.
Temika Cyber Graduation Certificate
Proof that you are ready to face the work world and formal exams.
Why Should You Master Kubernetes CKS?
🛡 Kubernetes Security is Becoming More Important
Kubernetes is used in almost all large companies, and CKS skills are the main differentiator in the field of Cloud & DevSecOps.
🌏 Globally Recognized Advanced Certification
CKS is the most prestigious Kubernetes security certification and is valued by global companies.
🧑💻 Bekal Praktis untuk Produksi
Helping you secure your real cluster, from RBAC, network policies, to runtime security.
Jadwal Pelatihan
Pelatihan dimulai
Program Akan dilaksanakan secara: –
Periode Kelas: –
Estimasi Durasi Belajar: –
Training Objectives
After successfully completing this course, participants will be able to:
-
Understanding Kubernetes security architecture.
-
Implementing RBAC & Network Policies to secure access.
-
Managing secrets & sensitive data securely.
-
Integrating security in the CI/CD pipeline.
-
Detecting & responding to runtime threats.
-
Securing the supply chain of container & image registries.
-
Preparing oneself for the official CKS Certification exam.
Syllabus
- Module 01 – Kubernetes Security Overview
- CKS Exam Domains
- Kubernetes Security Architecture
- Security Threat Landscape
- Module 02 – Cluster Hardening
- Securing API Server & etcd
- Role-Based Access Control (RBAC)
- Securing kubeconfig & TLS
- Module 03 – Linux & Node Security
- Securing Node OS
- AppArmor & SELinux
- Seccomp Profiles
- Module 04 – Kubernetes Networking Security
- Network Policies
- Ingress & Egress Control
- Securing Service-to-Service Communication
- Module 05 – Supply Chain Security
- Image Scanning
- Secure Registries
- Managing Trusted Sources
- Module 06 – Pod & Workload Security
- Pod Security Standards (PSS)
- Security Context & Capabilities
- Managing Secrets Securely
- Module 07 – Logging & Monitoring
- Audit Logs
- Event Monitoring
- Prometheus & Grafana Integration
- Module 08 – Runtime Security
- Falco & Threat Detection
- Container Runtime Security
- Incident Response Basics
- Module 09 – Evaluation
- Knowledge Quiz
- Hands-on Lab Test
- Module 10 – CKS Certification Preparation
- Exam Blueprint Review
- Time Management Strategy
- Practice Exam Simulation
- Module 11 – Final Project
- Secure Multi-tier Application Deployment
- Apply RBAC, Network Policies & Secrets
- Documentation & Presentation
Meet Your Expert
Trainer 1
Ethical Hacker
Trainer 2
Ethical Hacker
What Do They Say About This Training






Our Professional Certification
Get Special Prices During the Promotion
Early Bird I
- Intensive Training (5 Days)
- Official Training Material (e-Courseware)
- Official iLabs Access
- Certificate of Attendance
- CKS Certtification
FAQ
They have entrusted it to us