Become a Reliable Penetration Tester with Practical & Structured Training
Learn the latest techniques in ethical hacking, exploitation, and report writing to hone your skills in testing the security of corporate systems.

Join the Penetration Tester Training
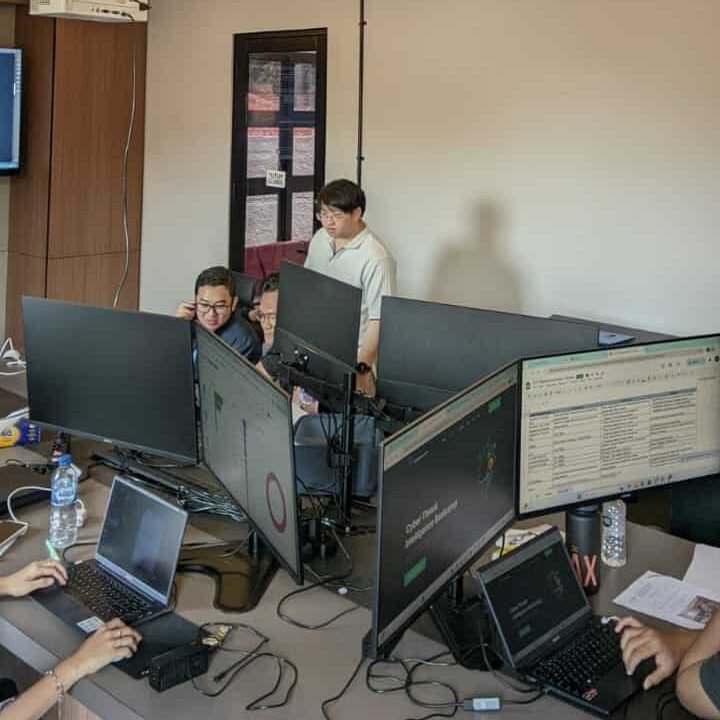
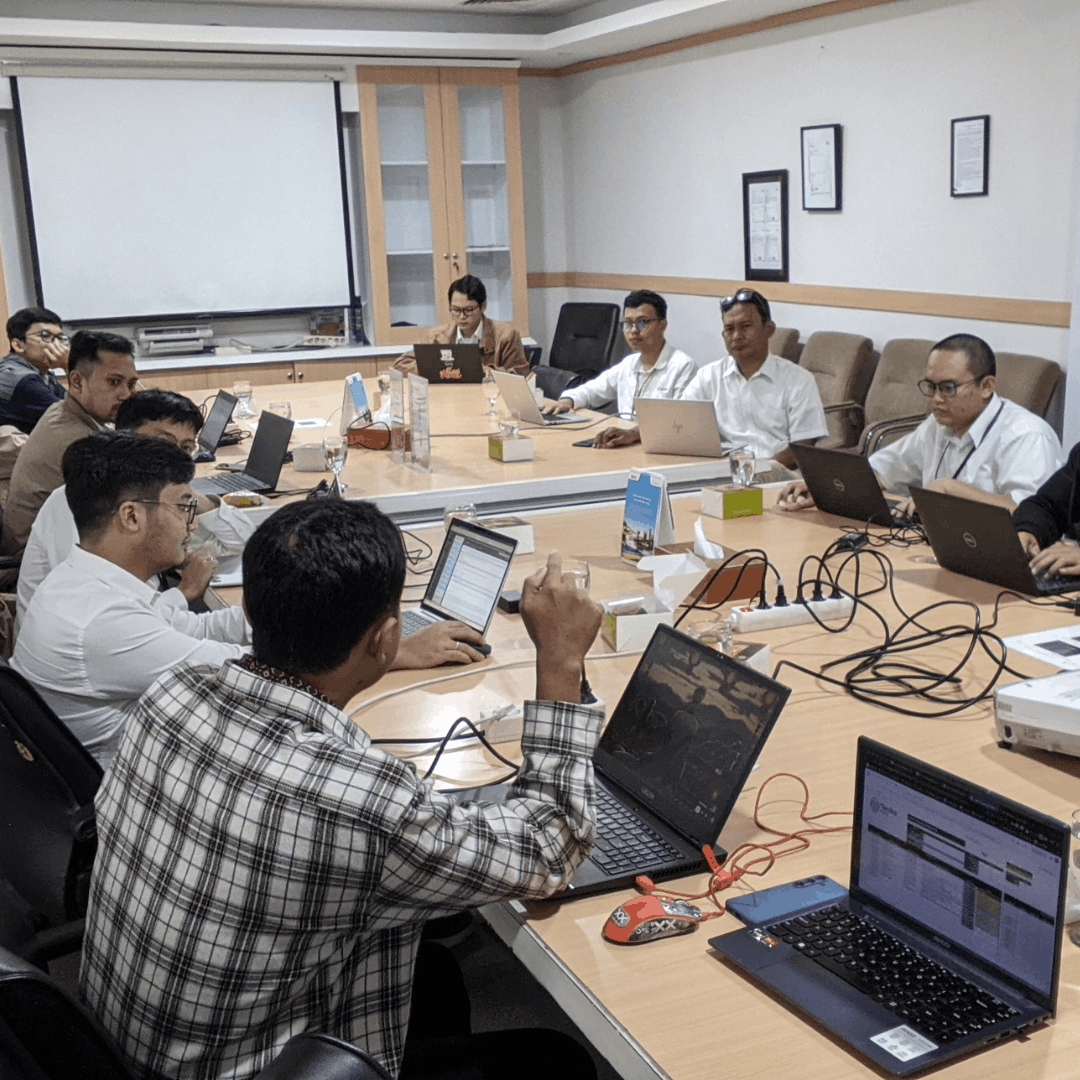
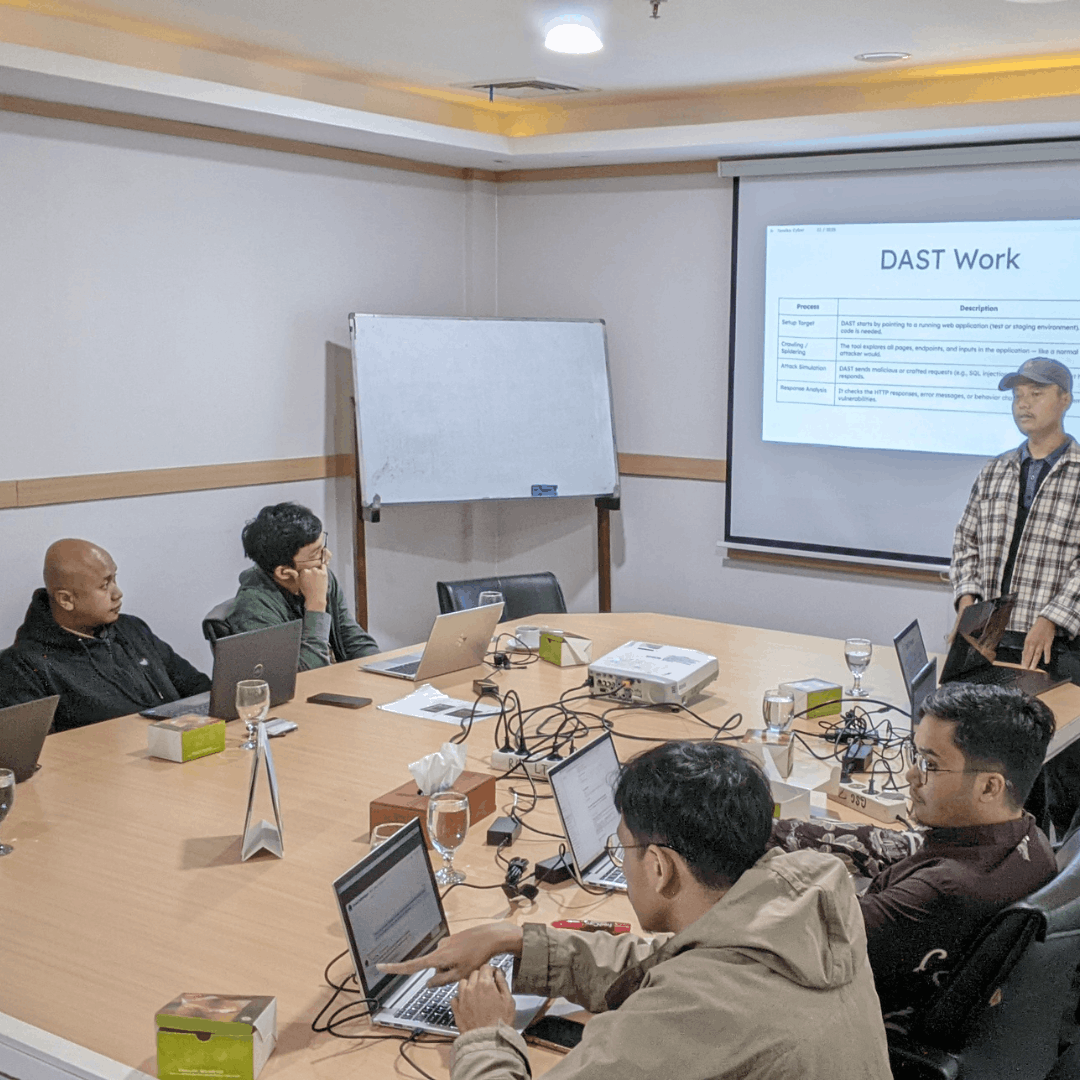
The Penetration Tester Training is designed to provide a deep understanding of the methods, techniques, and tools used by ethical hackers. Participants will be invited to engage in hands-on practice starting from reconnaissance, scanning, exploitation, to reporting. With a hands-on lab approach, participants are prepared to face real-world security testing challenges.
Benefits of Joining Training at Temika Cyber
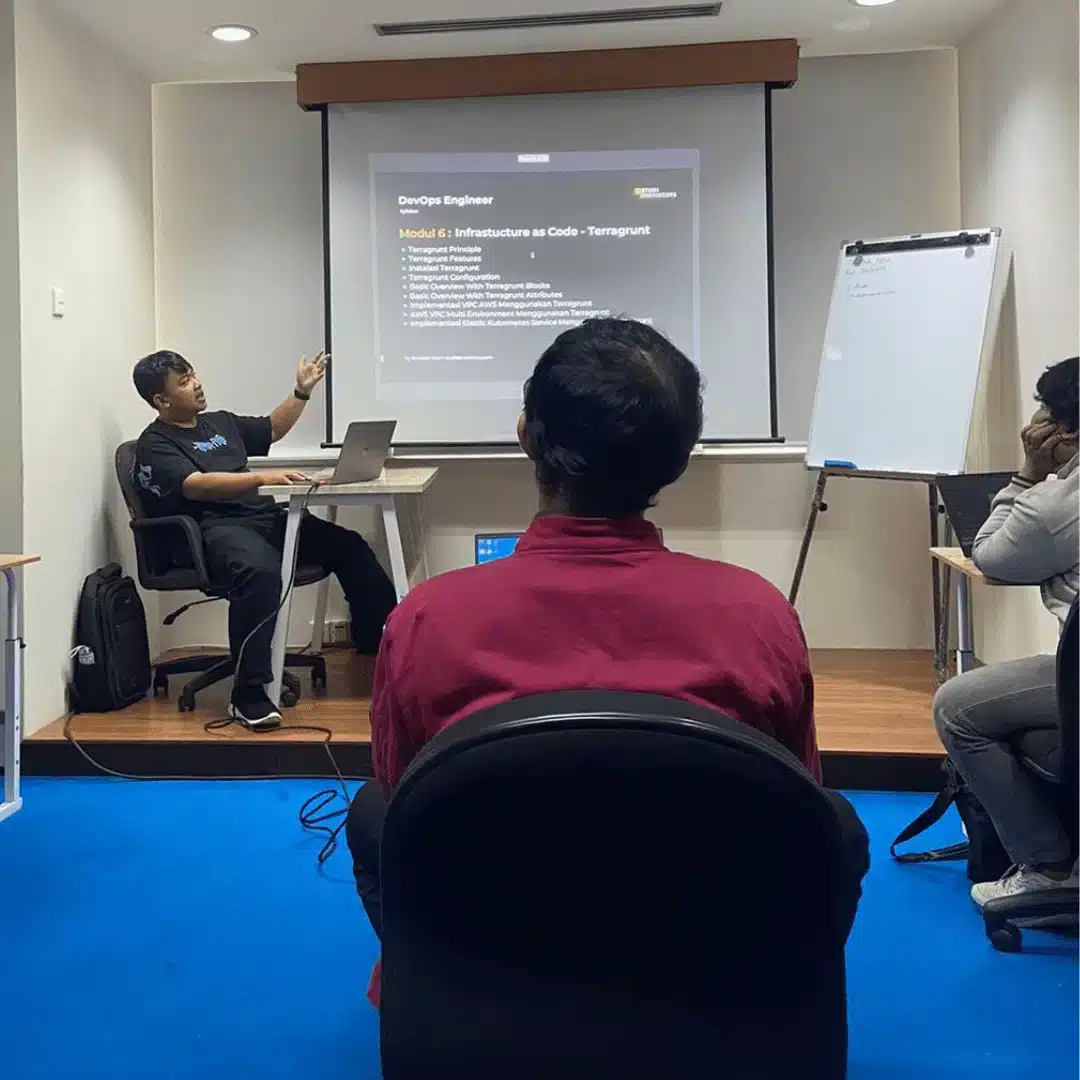
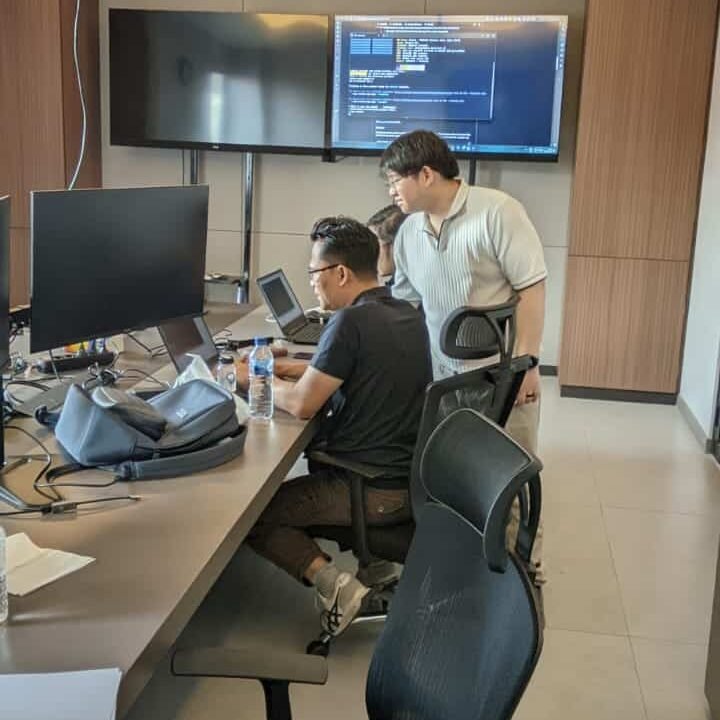
Hands-on Lab Intensive
Focus on hands-on practice with real attack scenarios.
Complete Material on Ethical Hacking
Including reconnaissance, exploitation, privilege escalation, to report writing.
Career Preparation & Certification
A strong foundation for the profession of penetration tester & global certification.
Real-World Case Simulation
Web application, internal network, and cloud system pentest scenario.
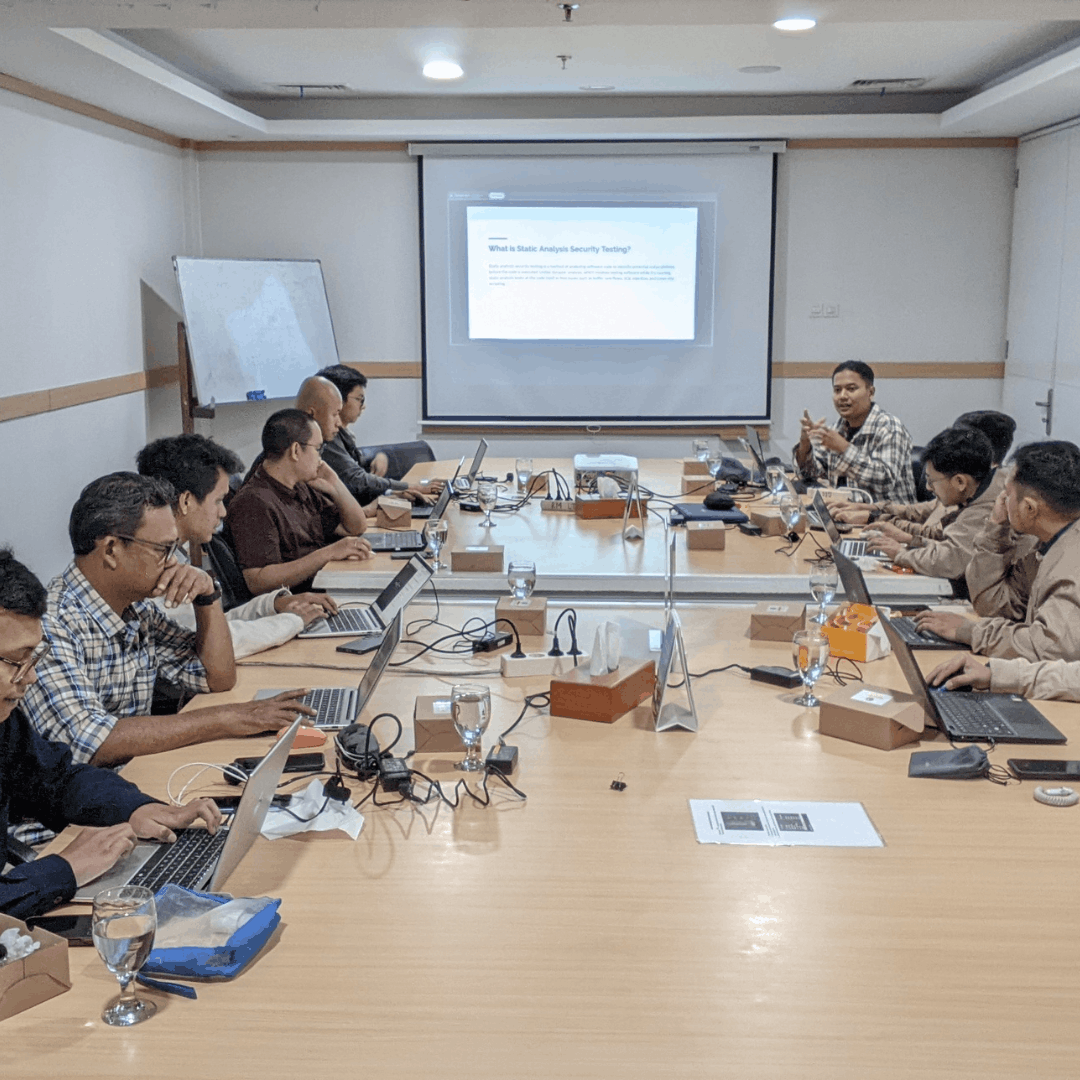
Experienced Instructor
Learn from cyber security practitioners with real experience in the industry.
Discussion of Popular Tools
Nmap, Burp Suite, Metasploit, Wireshark, Hydra, John the Ripper, dan lainnya.
Why Should We Master Penetration Testing?
🚀 Improving highly sought-after cybersecurity skills.
Penetration testing is one of the high-demand skills in the industry, as companies need professionals who can test security before hackers do it.
🎯 Able to test the security of applications, networks, and cloud infrastructure.
With this capability, you can perform comprehensive testing across various layers of the system, ranging from web applications, internal networks, to cloud-based services.
🙋A strong foundation for a career as an ethical hacker or red team specialist.
Mastering penetration testing opens up great opportunities for a career in cybersecurity, especially in strategic roles such as ethical hacker, red team, or security consultant.
Jadwal Pelatihan
Pelatihan dimulai
Program Akan dilaksanakan secara: –
Periode Kelas: –
Estimasi Durasi Belajar: –
Training Objectives
After successfully completing this course, participants will be able to:
-
Understanding end-to-end penetration testing methodology.
-
Mastering Reconnaissance & Information Gathering Techniques
-
Able to perform vulnerability scanning & exploitation.
-
Master privilege escalation and persistence.
-
Testing the security of web applications, networks, & cloud infrastructure.
-
Creating a professional report of the pentest results.
-
Preparing oneself for the role of a professional penetration tester.
Silabus
- Modul 1 – How To Become Cybersecurity Engineer
- Introduction to Cybersecurity
- Pros & Cons in Cybersecurity Field
- How to Become a Good Engineer
- Modul 2 – Introduction & Practical for GNU/Linux
- Linux Features & Distributions
- Working with Files, Contents & Directories
- Command & Argument
- User Management, Passwords & Profiles
- Modul 3 – Network Penetration Testing
- Basic Networking, OSI Layer
- IPv4/IPv6, CIDR, Subnetting
- Overview of Network Security
- Ports, Protocols & Analysis
- Kali Linux Installation
- Modul 4 – NMAP
- NMAP Basics
- SYN Scan, UDP Scan, OS Discovery
- Nmap Scripting Engine
- Modul 5 – Metasploit Framework
- Msfvenom & Metasploit Basics
- Windows Reverse TCP
- Auxiliary Scanner
- Hidden Bind TCP
- Post Exploitation Techniques
- Bypass UAC & Pass the Hash
- Modul 6 – Pentest Port Services
- FTP, SSH, Telnet Penetration Testing
- SMTP, NetBIOS & SMB Penetration Testing
- MsSQL & Other Common Services
- Modul 7 – Web Application Penetration Testing
- OWASP Top 10 Overview
- Burpsuite Fundamentals & Authentication Bypass
- HTML Injection & XSS (Basic to Advanced)
- Broken Access Control & Injection Attacks
- Security Misconfiguration & SSRF
- Vulnerable & Outdated Components
- Modul 8 – Bug Hunting
- Becoming a Good Bug Hunter
- Bug Hunter Mindset & Mind Map
- Legal Platforms for Bug Hunting
- Final Lab & Assessment
- Hands-on challenge combining reconnaissance, exploitation, and web attacks.
- Capture the Flag (CTF)-style mini project.
Meet Your Expert
Trainer 1
Ethical Hacker
Trainer 2
Ethical Hacker
What Do They Say About This Training






Our Professional Certification

Get Special Prices During the Promotion
Early Bird I
- Intensive Training (5 Days)
- Official Training Material (e-Courseware)
- Official iLabs Access
- Certificate of Attendance
FAQ
They have entrusted it to us