Certified SOC Analyst (CSA)
An intensive 5-day training to master Security Operations Center (SOC), threat analysis, and incident response professionally.
Attend the Certified SOC Analyst (CSA) Training.
The Certified SOC Analyst (CSA) training equips participants with the ability to professionally monitor, analyze, and respond to cyber incidents. This program comprehensively teaches the processes of a Security Operations Center (SOC), covering everything from log collection, threat analysis, to incident mitigation. With an intensive 5-day training, participants are prepared to tackle real-world cybersecurity challenges, utilizing SIEM and popular tools, and are ready to obtain the official EC-Council CSA certification.
Benefits of Participating in Training at Temika Cyber
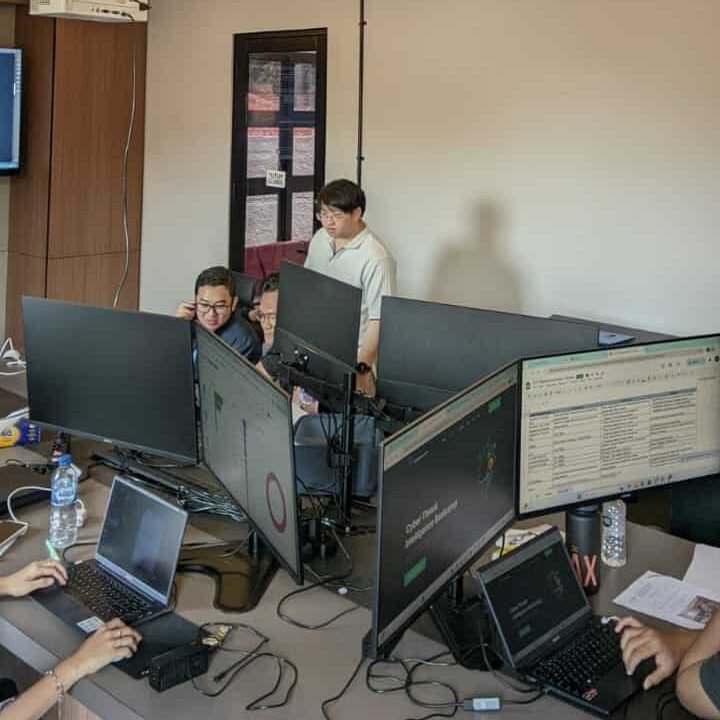
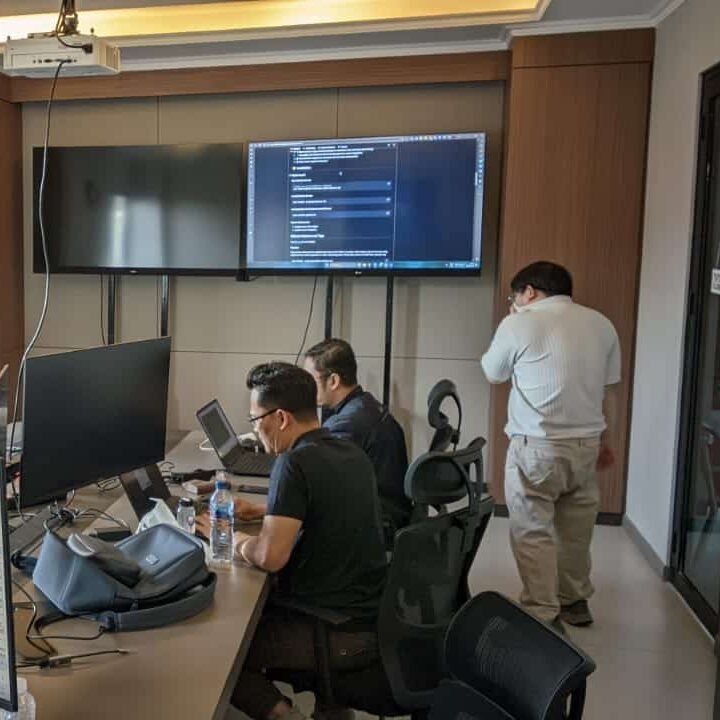
Hands-on SOC Lab & Monitoring Simulation
Realistic simulations in monitoring, detecting, and responding to incidents using SIEM and popular tools.
Official EC-Council CSA Material
The curriculum in accordance with EC-Council standards includes threat analysis, incident response, log monitoring, and basic forensics.
Exclusive Alumni Community
Join the Temika Cyber alumni community for discussions, material updates, experience sharing, and career opportunities.
Exam Preparation & Certification Path
Tips, practice questions, and guidance for facing the CSA exam to achieve official certification.
Career-Ready Skills & Networking
Master crucial skills: threat containment, forensic investigation, crisis communication, and compliance reporting.
Threat Intelligence Integration
Participants learn to utilize threat intelligence feeds to enhance the accuracy of incident detection and response.
Why is it Essential to Master CSA?
🚀 High Demand
SOC Analysts are highly sought after in the era of increasing cyber threats. Large companies and government organizations are looking for professionals who can monitor, analyze, and respond to threats swiftly.
💰 Promising Career Prospects
Profesional SOC di Indonesia maupun global memiliki peluang karier yang luas. Menguasai CSA meningkatkan peluang untuk mendapatkan posisi di SOC, Cybersecurity Analyst, atau Threat Intelligence Analyst dengan gaji menarik.
⚡ Crucial Skills & Real-Time Response
CSA gives participants the skills to detect threats, analyze logs, investigate incidents, and understand threat intelligence. With these skills, organizations can shift from being reactive to proactive when dealing with cyber attacks.
Jadwal Pelatihan
Pelatihan dimulai
Program Akan dilaksanakan secara: –
Periode Kelas: –
Estimasi Durasi Belajar: –
Training Objectives
After successfully completing this course, participants will be able to:
-
Understanding the roles and responsibilities of a SOC Analyst.
-
Mastering the process of monitoring and analyzing security logs.
-
Able to detect and respond to cyber incidents quickly.
-
Understanding various types of cyber attacks and indicators of compromise (IOC).
-
Using SIEM and popular SOC tools for security analysis.
-
Improving basic forensic investigation skills.
-
Preparing participants to be ready for the official CSA certification exam.
Sylllabus
- 09:00 – 09:30: Welcome & Course Introduction
- Introductions and setting expectations.
- Overview of CSA program and exam process.
- 09:30 – 10:45: Module 01 – SOC Concepts & Architecture
- Roles and responsibilities of a SOC Analyst.
- Understanding SOC operations, workflows, and levels (Tier 1-3).
- 10:45 – 11:00: Morning Break
- 11:00 – 12:30: Module 02 – Security Fundamentals
- OSI model, TCP/IP basics, and network protocols.
- Introduction to cybersecurity principles and frameworks.
- 12:30 – 13:30: Lunch Break
- 13:30 – 15:00: Module 03 – Threat Landscape Overview
- Common attack types and threat actors.
- Indicators of Compromise (IOCs) and Tactics, Techniques, and Procedures (TTPs).
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 04 – Hands-on: Basic SOC Monitoring
- Introduction to SIEM dashboards and alerts.
- Hands-on Lab: Monitoring sample network logs.
- 16:45 – 17:00: Day 1 Wrap-up & Q&A
- 09:00 – 10:30: Module 05 – Log Types & Sources
- Network, server, endpoint, and application logs.
- Hands-on Lab: Collecting and analyzing logs from multiple sources.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 06 – SIEM Fundamentals
- Introduction to SIEM tools and correlation rules.
- Hands-on Lab: Configuring alerts and dashboards.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 07 – Threat Intelligence Integration
- Using threat intelligence feeds to enrich alerts.
- Hands-on Lab: Mapping IOCs to real-world threats.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 08 – Case Study: Incident Detection
- Simulating real-world incidents for detection exercises.
- 16:45 – 17:00: Day 2 Wrap-up & Q&A
- 09:00 – 10:30: Module 09 – Incident Response Lifecycle
- Preparation, Identification, Containment, Eradication, Recovery, Lessons Learned.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 10 – Endpoint & Network Forensics
- Basic forensic investigation on endpoints and network devices.
- Hands-on Lab: Analyzing suspicious files and network traffic.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 11 – Malware Analysis Basics
- Identifying malware types and infection methods.
- Hands-on Lab: Safe environment malware analysis.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 12 – Case Study: Incident Handling
- Integrating detection, response, and analysis in realistic scenarios.
- 16:45 – 17:00: Day 3 Wrap-up & Q&A
- 09:00 – 10:30: Module 13 – Advanced SIEM & Correlation
- Advanced alert tuning and threat correlation.
- Hands-on Lab: Customizing rules and alerts for critical incidents.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 14 – Cloud & Hybrid Security Monitoring
- Monitoring cloud workloads and hybrid environments.
- Hands-on Lab: Cloud logs and alerting scenarios.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 15 – Threat Hunting Techniques
- Proactive hunting using SIEM and threat intelligence.
- Hands-on Lab: Hunting for hidden threats in simulated network.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 16 – Case Study: SOC Advanced Operations
- Practical exercises integrating monitoring, hunting, and response.
- 16:45 – 17:00: Day 4 Wrap-up & Q&A
- 09:00 – 10:30: Module 17 – Review of SOC & Incident Handling
- Recap of key concepts, workflows, and practical skills.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 18 – Threat Scenarios & Analysis
- Hands-on Lab: Analyzing complex threat scenarios.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 19 – Exam Tips & Practice Questions
- Discussion of exam format, practice questions, and scoring tips.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 20 – Mock Assessment & Q&A
- Scenario-based mock assessment to simulate real exam environment.
- 16:45 – 17:00: Course Wrap-up & Certification Guidance
Meet Your Expert
Trainer 1
Ethical Hacker
Trainer 2
Ethical Hacker
What Do They Say About This Training






Our Professional Certification
Get Special Prices During the Promotion
Early Bird I
- Intensive Training (5 Days)
- Official EC-Council Exam Voucher
- Official Training Material (e-Courseware)
- Official iLabs Access
- Certificate of Attendance
FAQ
They have entrusted it to us