EC-Council Certified Incident Handler (ECIH)
This official EC-Council training equips you with the framework, tools, and strategies to combat modern cyber attacks.

Participate in the EC-Council Certified Incident Handler (ECIH) training.
ECIH is an official program from the EC-Council designed to train professionals in identifying, handling, and responding to cybersecurity incidents. Participants will learn global best practices in Incident Response (IR), ranging from early detection, malware handling, ransomware management, to post-incident recovery.
Benefits of Participating in Training at Temika Cyber
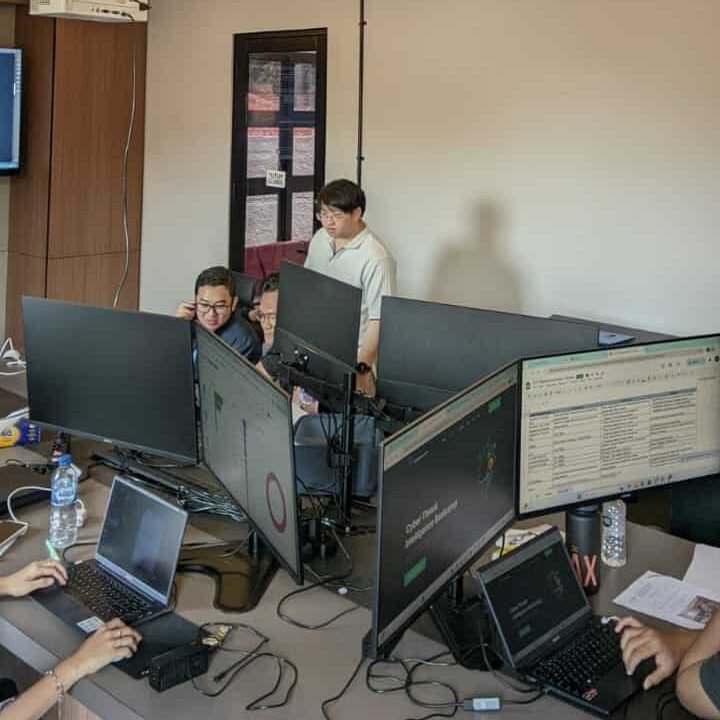
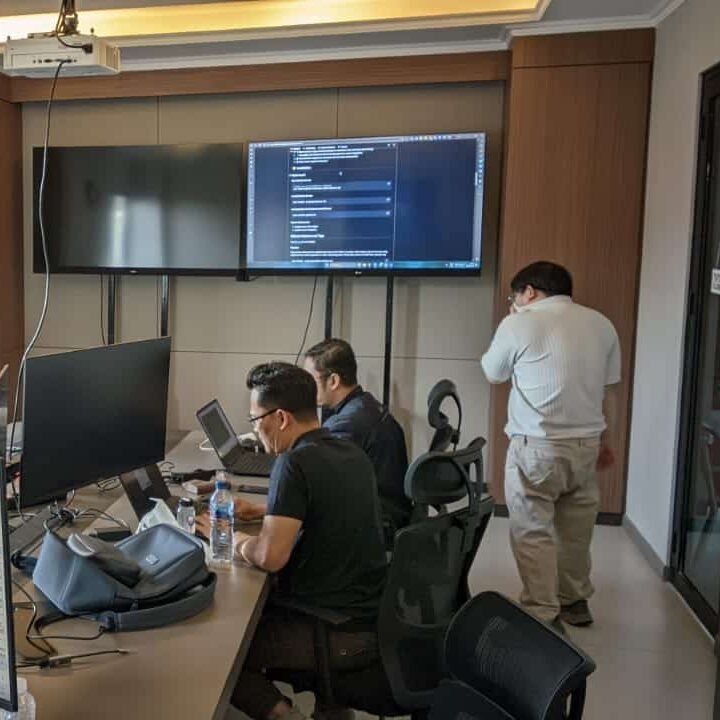
Hands-on Threat Intelligence Lab
Simulation of real incidents: malware outbreak, phishing attack, ransomware infiltration.
Official EC-Council Materials
The latest curriculum is aligned with EC-Council standards, focusing on the phases of Incident Response: preparation, detection, containment, eradication, recovery, and lessons learned.
Exclusive Alumni Community
Join the Temika Cyber alumni community for discussions, material updates, experience sharing, and career opportunities.
Exam Preparation & Certification Path
A comprehensive guide, practice questions, and strategies for facing the ECIH examination up to official certification.
Career-Ready Skills & Networking
Master crucial skills: threat containment, forensic investigation, crisis communication, and compliance reporting.
Real-World Tools & Frameworks
Utilize popular incident response tools such as SIEM, forensic tools, and frameworks such as NIST, ISO, and SANS.
Why is it necessary to master ECIH?
🚀 High-Quality Professional IR Request
Global companies increasingly require incident handlers to protect data and business operations.
💰 Promising Career Prospects
The role of Incident Handler & Response Specialist has become one of the high-paying positions in global cybersecurity.
⚡ The Threat is Becoming Increasingly Complex
Starting from ransomware, insider threats, to APT attacks. With ECIH, you are prepared to face proactive threats.
Training Objectives
Upon successfully completing this course, participants will be able to:
-
Understanding the concepts of incident response in accordance with EC-Council standards & international frameworks (NIST, SANS, ISO).
-
Detecting and analyzing cyber incidents including malware, phishing, ransomware, and network attacks.
-
Handling incidents with proactive methods, ranging from containment, eradication, to recovery.
-
Prepare incident reports and documentation professionally for compliance, audits, and internal evaluations.
-
Utilizing modern IR tools and frameworks for field practice, threat hunting, and forensic investigation.
-
Developing career skills as an Incident Handler or SOC Analyst with abilities in analysis, communication, and team coordination.
Sylllabus
- 09:00 – 09:30: Welcome & Course Introduction
- Introductions and setting expectations.
- Overview of ECIH program and exam process.
- 09:30 – 10:45: Module 01 – Fundamentals of Incident Handling
- Key concepts of incident response & handling.
- Incident types and lifecycle.
- Incident handling framework: NIST, SANS.
- 10:45 – 11:00: Morning Break
- 11:00 – 12:30: Module 02 – Preparation & Planning
- Establishing policies and procedures.
- Roles & responsibilities of the incident response team.
- Developing incident response plans.
- Hands-on Lab: Creating an incident response plan for a sample organization.
- 12:30 – 13:30: Lunch Break
- 13:30 – 15:00: Module 03 – Detection & Analysis
- Identifying indicators of compromise (IOCs).
- Monitoring network and system logs.
- Hands-on Lab: Using SIEM tools for log analysis and detection.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 04 – Incident Reporting & Documentation
- Documenting incidents for compliance and auditing.
- Communication protocols during incidents.
- Hands-on Lab: Drafting an incident report and escalation workflow.
- 16:45 – 17:00: Day 1 Wrap-up, Q&A
- 09:00 – 10:30: Module 05 – Malware Analysis & Containment
- Types of malware and infection vectors.
- Malware lifecycle and behavior analysis.
- Hands-on Lab: Isolating and analyzing a malware sample in a sandbox environment.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 06 – Phishing & Social Engineering
- Understanding phishing techniques and social engineering attacks.
- Hands-on Lab: Simulating phishing attack detection and response.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 07 – Email Security Controls
- Email filtering and authentication methods (SPF, DKIM, DMARC).
- Mitigation strategies and best practices.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 08 – Case Study: Malware & Phishing Incident Response
- Applying learned techniques to a realistic scenario.
- 16:45 – 17:00: Day 2 Wrap-up, Q&A
- 09:00 – 10:30: Module 09 – Network Attacks & Intrusion Detection
- Common network attacks (DDoS, port scans, MITM).
- Hands-on Lab: Detecting network attacks using IDS/IPS tools.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 10 – Web Application Attacks
- Understanding SQL injection, XSS, CSRF.
- Hands-on Lab: Simulating and mitigating web application attacks.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 11 – Log Analysis & Forensic Techniques
- Collecting evidence from servers and applications.
- Hands-on Lab: Conducting forensic analysis on compromised web server.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 12 – Incident Containment & Eradication
- Strategies to contain attacks and remove threats.
- Hands-on Lab: Containing an ongoing network intrusion.
- 16:45 – 17:00: Day 3 Wrap-up, Q&A
- 09:00 – 10:30: Module 13 – Ransomware Handling & Mitigation
- Ransomware types, attack vectors, and recovery methods.
- Hands-on Lab: Containment and recovery simulation.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 14 – Cloud Security Incidents
- Incident response for IaaS, PaaS, SaaS environments.
- Hands-on Lab: Investigating cloud security breaches.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 15 – Mobile & IoT Security Incidents
- Handling attacks on mobile devices and IoT networks.
- Hands-on Lab: Simulating mobile malware incident response.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 16 – Case Study: Multi-Vector Incident Handling
- Integrating malware, network, cloud, and mobile incident response.
- 16:45 – 17:00: Day 4 Wrap-up, Q&A
- 09:00 – 10:30: Module 17 – Recovery & Business Continuity
- Developing recovery strategies and business continuity plans.
- Hands-on Lab: Drafting disaster recovery plan for simulated incident.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 18 – Lessons Learned & Post-Incident Review
- Conducting post-mortem analysis.
- Identifying gaps and improving IR processes.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 19 – Incident Handling Best Practices & Compliance
- Regulatory requirements, standards (ISO 27001, GDPR).
- Reporting to management and external parties.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 20 – Exam Preparation & Simulation
- Review key concepts, practice questions, exam tips.
- Hands-on Lab: Mock scenario-based assessment.
- 16:45 – 17:00: Course Wrap-up, Q&A, Certification Guidance
Meet Your Expert
Trainer 1
Ethical Hacker
Trainer 2
Ethical Hacker
What Do They Say About This Training?






Our Professional Certification
Obtain Special Prices During the Promotion
Early Bird I
- Intensive Training (5 Days)
- Official EC-Council Exam Voucher
- Official Training Material (e-Courseware)
- Official iLabs Access
- Certificate of Attendance
FAQ
Mereka Telah Mempercayakannya Kepada Kami