Certified Network Defender (CND)
An official program from the EC-Council designed to equip IT professionals with the skills to maintain, detect, and respond to network threats. This training prepares you to face modern network security challenges with a defensive, proactive, and globally standard approach.
Join the Certified Network Defender (CND) training.
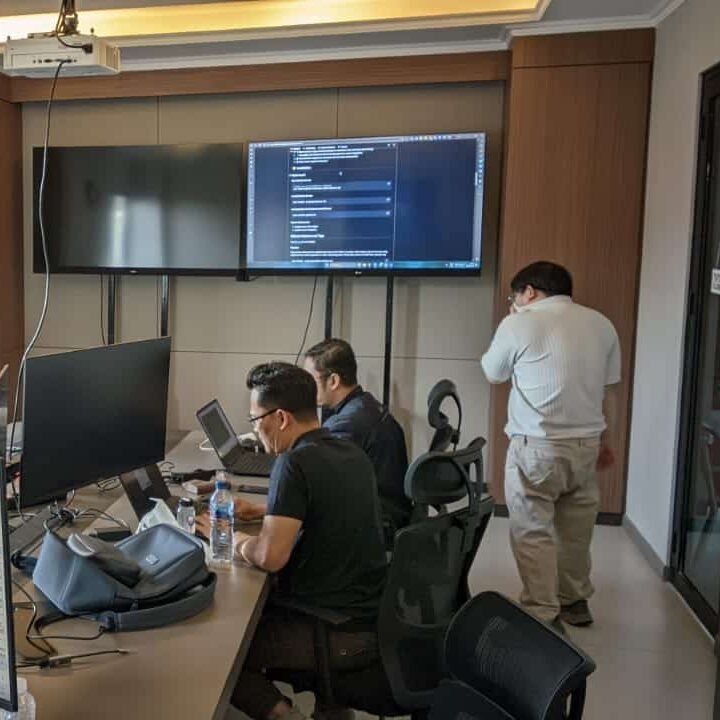
In an era of increasingly complex cyber attacks, companies need reliable defenders to protect their digital assets. Certified Network Defender (CND) offers a comprehensive curriculum that includes network security architecture, intrusion detection, log analysis, system hardening, and incident response strategies. Through a combination of theory and hands-on labs, participants will understand how hackers operate, while mastering effective defense techniques to safeguard the company's network infrastructure.
Benefits of Joining Training at Temika Cyber
Hands-on Network Defense Lab
Hands-on practice: firewall configuration, IDS/IPS, VPN, and SIEM.
Official EC-Council Materials
The curriculum complies with CND standards, covering modern attacks & defense tools.
Incident Detection & Response
Log investigation techniques, traffic analysis, and mitigation procedures.
Exam Preparation & Certification Path
Practice questions, exam strategies, and tips for facing official CND certification.
Career-Ready Skills & Networking
Practical skills: network hardening, cloud security, network forensics, basic threat intelligence.
Real-World Tools & Frameworks
Use popular tools: Wireshark, Snort, Suricata, Splunk, and other open-source frameworks.
Why Should One Master CND?
🚀 High Professional Demand
Network security engineers and defenders are in high demand in various industries.
💰 Career Prospects & Competitive Salaries
The profession of a network defender is known for its promising average salary.
⚡ Real Threat
Hackers exploit network vulnerabilities, while CND equips skills to close the gaps.
Jadwal Pelatihan
Pelatihan dimulai
Program Akan dilaksanakan secara: –
Periode Kelas: –
Estimasi Durasi Belajar: –
Training Objectives
After successfully completing this course, participants will be able to:
-
Understanding the basic concepts of network security and defense-in-depth.
-
Mastering monitoring, logging, and traffic analysis techniques.
-
Knowing how IDS/IPS, firewalls, and VPNs work.
-
Applying hardening to systems and network devices.
-
Performing incident response and basic forensics.
-
Integrating threat intelligence into defense strategy.
-
Preparing participants for the official Certified Network Defender (CND) exam.
Sylllabus
- 09:00 – 09:30: Welcome & Course Introduction
- Introductions and expectations.
- Overview of CND certification and exam process.
- 09:30 – 10:45: Module 01 – Network Fundamentals & Defense-in-Depth
- Basics of networking and protocols.
- Defense-in-depth strategy for enterprise security.
- 10:45 – 11:00: Morning Break
- 11:00 – 12:30: Module 02 – Network Security Threat Landscape
- Types of attacks: malware, phishing, DoS, MITM, insider threats.
- Understanding threat actors and motives.
- 12:30 – 13:30: Lunch Break
- 13:30 – 15:00: Module 03 – Network Defense Essentials
- Network security architecture.
- Hands-on Lab: Configuring basic security on network devices.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 04 – Administrative Network Security
- Policy creation and user access control.
- Hands-on Lab: Implementing network security policies.
- 16:45 – 17:00: Day 1 Wrap-up & Q&A
- 09:00 – 10:30: Module 05 – Perimeter Security Fundamentals
- Firewalls, IDS/IPS, and network segmentation.
- Hands-on Lab: Firewall configuration basics.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 06 – Intrusion Detection & Prevention
- Snort, Suricata, and IDS/IPS methodologies.
- Hands-on Lab: Deploying IDS for packet analysis.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 07 – VPN & Secure Remote Access
- Virtual Private Networks, tunneling, and encryption protocols.
- Hands-on Lab: VPN setup for secure communication.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 08 – Case Study: Perimeter Breach Defense
- Scenario-based exercise on defending network perimeter.
- 16:45 – 17:00: Day 2 Wrap-up & Q&A
- 09:00 – 10:30: Module 09 – Network Monitoring & Traffic Analysis
- Packet capture, flow analysis, and anomaly detection.
- Hands-on Lab: Wireshark traffic monitoring.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 10 – Log Management & SIEM
- Centralized logging, ELK stack, and Splunk fundamentals.
- Hands-on Lab: Setting up log collection and SIEM alerts.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 11 – Endpoint Security & Hardening
- Hardening operating systems and applications.
- Hands-on Lab: Applying security baselines to endpoints.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 12 – Case Study: Incident Monitoring
- Simulated SOC environment for monitoring suspicious activity.
- 16:45 – 17:00: Day 3 Wrap-up & Q&A
- 09:00 – 10:30: Module 13 – Network Hardening & Patch Management
- Securing routers, switches, and servers.
- Hands-on Lab: Applying patches and security configs.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 14 – Wireless Network Security
- WPA3, rogue AP detection, and wireless monitoring.
- Hands-on Lab: Securing Wi-Fi networks.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 15 – Cloud & Virtualization Security
- Securing cloud workloads and virtualized environments.
- Hands-on Lab: Cloud instance security configuration.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 16 – Case Study: Hybrid Environment Defense
- Defending a mixed on-premises and cloud environment.
- 16:45 – 17:00: Day 4 Wrap-up & Q&A
- 09:00 – 10:30: Module 17 – Incident Response Planning
- IR lifecycle: Preparation, Detection, Containment, Eradication, Recovery.
- Hands-on Lab: Simulated incident response exercise.
- 10:30 – 10:45: Morning Break
- 10:45 – 12:15: Module 18 – Network Forensics Basics
- Collecting and analyzing network-based evidence.
- Hands-on Lab: Network forensic case analysis.
- 12:15 – 13:15: Lunch Break
- 13:15 – 15:00: Module 19 – Exam Tips & Practice Questions
- Discussion of exam format, practice questions, and strategies.
- 15:00 – 15:15: Afternoon Break
- 15:15 – 16:45: Module 20 – Mock Assessment & Q&A
- Scenario-based mock exam simulation.
- 16:45 – 17:00: Course Wrap-up & Certification Guidance
Meet Your Expert
Trainer 1
Ethical Hacker
Trainer 2
Ethical Hacker
What Do They Say About This Training






Our Professional Certification
Get Special Prices During the Promotion
Early Bird I
- Intensive Training (5 Days)
- Official EC-Council Exam Voucher
- Official Training Material (e-Courseware)
- Official iLabs Access
- Certificate of Attendance
FAQ
Mereka Telah Mempercayakannya Kepada Kami

































Trending Now
Contact Us